I published this map analysis in September 2023, one month prior to the Hamas Terrorist Attack in Israel. Since that time the Quadraplex relationship solidified into a geopolitical alliance, pledging mutual security support, including: the supply of munitions, weaponry, and military equipment. It is especially noteworthy in the face of the 2026 strategic bombing campaign, Operation EPIC FURY. Making Iran combat ineffective is an accomplishment of major importance to the allied western nations.

Is the Islamic Regime’s Refusal to Capitulate Unreasonable?
Introduction
The catchphrase, “beauty is in the eyes of the beholder,” sets the tone for examining the term, “unreasonable.” What seems as unreasonable to one person (organization), may appear reasonable to someone else, and vice versa.
As of March 11, 2026, the U.S. Navy and Air Force, along with the Israeli Air Force, have flown more than 6,000 strike sorties against 16,000 targets inside Iran’s Islamic Republic, as well as, key maritime targets. With Iran being on the receiving end of Operation EPIC FURY’s bombing campaign, the Islamic Regime’s refusal to capitulate seems unreasonable to the global community.
As duplicitous as the Islamic Regime is known to be, it’s refusal to surrender should not be seen as a patriotic or religious act; it’s merely buying time to concoct a plan of further retaliation. The Islamic Regime cares nothing about being reasonable or unreasonable; neither state enters into their calculus.
America has seen this sort of rigid defiance before by the Japanese and Germans in World War II, and by the Vietnamese Communists in Hanoi during the Vietnam War. All three of these foes were seen by Washington, D.C. leadership as being unreasonable. How America and her allies responded in the face of seemingly unreasonable behavior, varied for each of the three countries. In Germany, as long as Adolf Hitler was in-charge, unconditional surrender was off the table. Even after removal of Japan’s military government leaders, they were still hesitant to surrender unconditionally. The hardliner Hanoi Communists refused to accept any sort of capitulation, and were unreasonable during the Paris Peace Conference. They were forced back to the bargaining table as a result of America’s Christmas Bombing Offensive known as Operation LINEBACKER II. But, Hanoi never surrendered anything.
The Utility of Declaring an Entity Reasonable or Unreasonable
Unless both parties in a dispute have the same or similar value system, determining reasonability is a zero sum game. As long as Party A chooses to label Party B as unreasonable, Party A has three choices: keep doing the same thing, hoping Party B will someday become reasonable, or change tactics to something that resolves the impasse, or reassess whether the situation is even worth pursuing, and walk away if it’s not. A real-life, high stakes unreasonableness situation is worth discussing here as an example.
In my book, “The 99th Strategic Reconnaissance Squadron: The Air Force’s Story of Unmanned Reconnaissance in the Vietnam War,” I covered a situation involving reasonableness vs. unreasonableness in the run-up to the Vietnam War.
In 1961, President John F. Kennedy issued National Security Action Memorandum (NSAM) 55, which directed the Joint Chiefs of Staff to conduct their duties as “more than military men,” by taking-in the geopolitical realities underlying national security issues. NSAM 55 remained actionable throughout the Vietnam War, and was applicable if the three Vietnam Era Presidents (Johnson, Nixon, Ford), wanted to use it. As it turned out, each President did as he pleased, and NSAM 55 remained on the shelf, unused. Although NSAM 55 implied a standard of reasonableness, each President judged it by his own barometer.
Maxwell Taylor, Chairman of the Joint Chiefs of Staff from 1960-1964, was the first senior military officer to put NSAM 55 to the test. He demonstrated good political chops, and easily navigated the halls of power in Washington, D.C., and the Pentagon. Simply put, Taylor fit well with NSAM 55.
On the Eve of the Vietnam War
In early 1964, the National Command Authority (President Johnson, Defense Secretary Robert McNamara, and General Taylor ) were receiving a steady stream of reports from Henry Cabot Lodge, U.S. Ambassador in Saigon, and his military counterpart in-charge of America’s local military assistance command, that the Saigon government and its military forces were struggling under a multitude of self-inflicted problems.
Throughout 1964, U.S. military presence in and around South Vietnam numbered about 25,000 personnel representing the Navy, Army and Air Force. The vast majority of these G.I.s were special operation forces working as advisors to the South Vietnamese military. They were not conducting independent combat operations, but they accompanied their Vietnamese counterparts on offensive missions.
The American military leaders in-country and the Embassy diplomats, all sensed it was only a matter of time before the North Vietnamese and the South’s Viet Cong significantly upped their game.
In response to multiple intelligence reports coming into the National Command Authority from both the State Department and the Pentagon, a new NSAM was issued. This new memorandum directed the Admiral over the Pacific Command to develop a comprehensive list of strike targets in North Vietnam.
There were no hard plans to conduct airstrikes in North Vietnam. The target list was developed for a rainy day. The Joint Chiefs of Staff were directed to evaluate the list, and develop a plan to implement an airstrike campaign, if needed.
When the Joint Staff released the airstrike plan, it fell to the JCS Chairman, Maxwell Taylor, to prepare an executive briefing for the National Command Authority and other key players. The original recommendation was to exhaust every target on the strike list without letting up. To Taylor’s mind, war requires pressing the advantage until the foe either surrenders, or becomes combat ineffective.
Taylor Applies the Tenets of NSAM 55
It was Taylor’s desire to comply with NSAM 55 which led him to soften the tone of his May 1964 JCS recommendation. The JCS’ original wording stated the bombing campaign represented by the 94-Targets List was designed to eliminate (through destruction by bombing) North Vietnam’s physical ability to support the Viet Cong and Pathet Lao in waging an insurgency.
The plan of action was revised to specify one unannounced, surprise attack with a huge ordnance load covering major targets across the country.
Taylor’s rewording sought to look at things from a political standpoint based on the reactions of a “reasonable” man to a major, multi-pronged air attack on his homeland for supporting the destabilizing, political goals, and insurrection of groups in adjacent sovereign countries. The Johnson Administration bought-in to the “reasonable man” theory.
To a certain extent, President Johnson’s own political style of arm-twisting and backing the other guy into a corner, played a role in the Vietnam War policies adopted by the White House. Throughout Johnson’s tenure on Capitol Hill as a Congressman and Senator , he counted on his opponent’s reasonableness when confronted with the opportunity to either acquire something they wanted, or avoid something they did not want.
Western politicians believe that every reasonable man has his price. Johnson, and his colleagues, failed to understand that as far as North Vietnam was concerned, the struggle by the Viet Cong, and Pathet Lao (and the Khmer Rouge later on), put them all in the same boat. These communist-aligned insurgencies, as well as North Vietnam, all viewed the Saigon-based democratic government as being “on-the-wrong-side.”
I have always felt that as long as someone is not a psychopath or sociopath, and has a reasonable level of maturity, it puts them in the largest segment of the global population, or what I call the reasonable and rational majority. Being in the majority has nothing to do with right or wrong, moral or immoral, nor does it mean a group member is always reasonable & rational; we all have our days.
The majority of the population covers a broad spectrum of society, to include prominent people in the 1960s, such as: Dwight Eisenhower, John F. Kennedy, Ho Chi Minh, Nikita Khrushchev, and Fidel Castro. Each of these well-known leaders had many followers, and many detractors. Clearly, what one of these men felt was rational behavior on a given day, might be viewed by one of the others as irrational, or unreasonable.
Robert McNamara and “The Fog of War”
An award-winning 2003 documentary entitled, “The Fog of War,” illustrates a real-life case of political reasonability experienced by Robert McNamara, the Defense Secretary during the Vietnam War. The Fog of War convincingly presents 11 truths he coined about national security, foreign policy & war.
Truth #2 states: “you cannot count on rationality (reasonableness) to save the day.” This is 100% applicable to the frustration with both Hanoi’s and Tehran’s “never say die” behavior in the face of mounting military pressure. To American leadership, both regimes were clearly being irrational & unreasonable. McNamara arrived at his opinion about rationality and reasonableness based on his experience with the 1962 Cuban Missile Crisis; an encounter 30 years later would completely overturn his view.
After resolving the impasse with Moscow about the missiles in Cuba, and tension abated, McNamara and other Kennedy Administration officials thought rational and reasonable behavior had won the day. In 1993 McNamara attended a global symposium where he ran into Fidel Castro. Civility & restraint were maintained by both men as they chatted for a few minutes.
McNamara commented to El Presidente that a near catastrophe was averted in 1962 when cooler heads prevailed. Castro said nuclear annihilation came a lot closer than anyone knew, including McNamara and his cohorts. McNamara’s interest was piqued , and he inquired as to Castro’s meaning. Castro told him that contrary to popular belief, when Washington thought they had nipped things in the bud, there were actually 126 nuclear warheads already on the island! Until that moment in 1993, McNamara & the U.S. Government thought the warheads were still on a ship at sea, and had been turned back as a result of the U.S. Navy’s blockade of Cuba.
McNamara was stunned! He quickly told Castro he had three questions: 1.) Did Castro know the warheads were there the whole time? 2.) What was Castro’s greatest concern throughout the Crisis? 3.) After the Crisis became public knowledge, and negotiations commenced between the White House and the Kremlin, what was Castro’s advice to Khrushchev?
Castro admitted he knew all along the warheads were on the island. His greatest fear was an all-out conventional air, land and sea attack on Cuba by the United States. If this had occurred, his recommendation to Premier Khrushchev was to launch a nuclear attack on America from Cuba.
Castro’s revelation changed McNamara’s mind about a man’s reasonable behavior in the face of adversity. Whereas, Hanoi’s unreasonable behavior was seen by McNamara and others as a one-off anomaly, it was instead, a validation that rational or reasonable behavior is not universally defined.
Johnson, McNamara and General Taylor’s failure to comprehend Hanoi’s brand of reasonableness, led to 58,000 American deaths, and more than a million Vietnamese casualties. The Johnson Administration’s misreading of the conflict’s geopolitics led to the U.S.’ accelerated departure, leaving numerous unresolved issues at War’s end.
Not understanding North Vietnam’s indifference led to the ineffective ROLLING THUNDER bombing campaign, starting in March 1965, and ran for three years. To the Washington establishment, Hanoi’s seeming unreasonable behavior was just one of the manifestations that defied western logic.
The Islamic Republic’s Disinterest in an Unconditional Surrender
The “talking heads” on network news are speaking-out of both sides of their mouths regarding Operation EPIC FURY. On the one hand, Trump started a war when there is supposedly no imminent threat from Iran, which is a ridiculous assertion. On the other hand, the same group of reporters are incredulous that under a massive onslaught of destruction, why does the Islamic Regime allow it to continue and not sue for peace?
There is a simple answer to Iran’s seeming unreasonable indifference to the destruction. Above any other reason for the despotic regime’s behavior, is the survival of the Islamic hardliners controlling the country.
Most people fail to recognize that the Islamic Regime has been planning and preparing for this day for 47 years. The organization pulling the strings of power is not part of the public-facing official government. It’s a shadow government that was created to rigidly control the country at every level of government, and all major civil and commercial institutions, and the largest industry segments, such as, banking, manufacturing, agriculture, transportation, the education sector and the oil industry, to name a few. This ruling, shadow institution is known as The Bayt (pronounced like “bait” used for fishing). The Bayt is designed to survive.
The United Against a Nuclear Iran (UANI) organization
The UANI published a landmark report in February 2026 entitled, “Unmasking the Bayt: Inside the Supreme Leader’s Office, the Hidden Nerve Center of the Islamic Republic.” The report was written by two Iranian-Americans PhDs,, Saeid Golkar, and Kasra Aarabi, the founders of UANI.
Golkar and Aarabi said in their Report about the Bayt, “What has become the most powerful political entity in the Islamic Republic has its roots in Shia Islam’s convention surrounding the Bayt-e Ulema (House of Religious Scholars).” The Bayt is an important part of Shia Islamic doctrine that is centuries old.
In simple terms, senior Shia clerics who have been elevated to ayatollah status (does not necessarily mean they are a supreme leader), and have developed a publicly visible following, are bestowed with the title of “Marja-e-Taqhlid;” this stands for “source of emulation.” Once a cleric becomes a Marja-e-Taqhlid, they are entitled to establish a Bayt. At this point, the Bayt is the nucleus of the cleric’s paid office staff. Bayts commonly employ male members of a cleric’s family. Prior to Iran’s 1979 Revolution, a Bayt office was strictly for religious purposes.
Evolution of the Islamic Republic’s Bayt
In 1979, upon the arrival of the exiled Ayatollah Ruhollah Khomeini in Iran, he was designated as the first supreme leader (until March 8, 2026, there had only been two). Khomeini’s Bayt was with him throughout his exile in France. Due to Khomeini’s unconventional status in exile, his Bayt necessarily assumed quite a few secular duties (i.e.; security, travel & transportation, event planning, etc.), as well as a Bayt’s more traditional religious duties.
When Ayatollah Ruhollah Khomeini died 10 years later in 1989, it was assumed that his son would become the next supreme leader; it never happened. His son, Ahmad, was outmaneuvered by a conspiracy of Hashemi Rafsanjani and the now deceased Ayatollah Ali Khamenei. Khamenei became the supreme leader and Rafsanjani became President. It was Khamenei, with Rafsanjani’s support, who began transforming the Bayt he inherited into a formidable base of political control. The Bayt eventually numbered more than 4,000 staffers and a network of over 40,000 independent operatives.
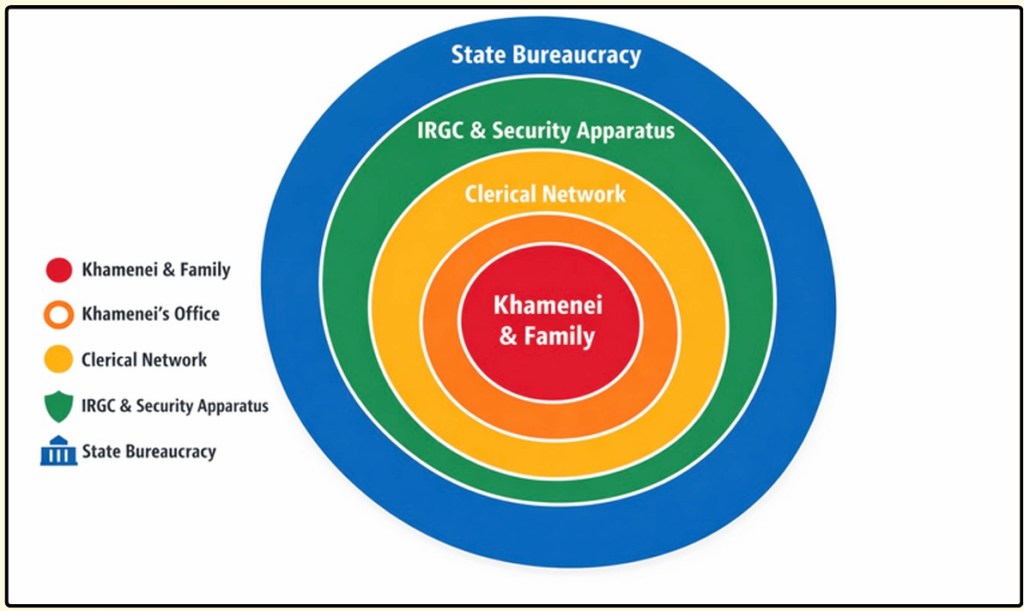
Shown below is how Khamenei’s Bayt was organized prior to his death a few weeks ago. All functions shown in boldface type are direct members of the Bayt. Although it’s not shown here, each non-Bayt institution has at least one commissar overseer who belongs to the Bayt.
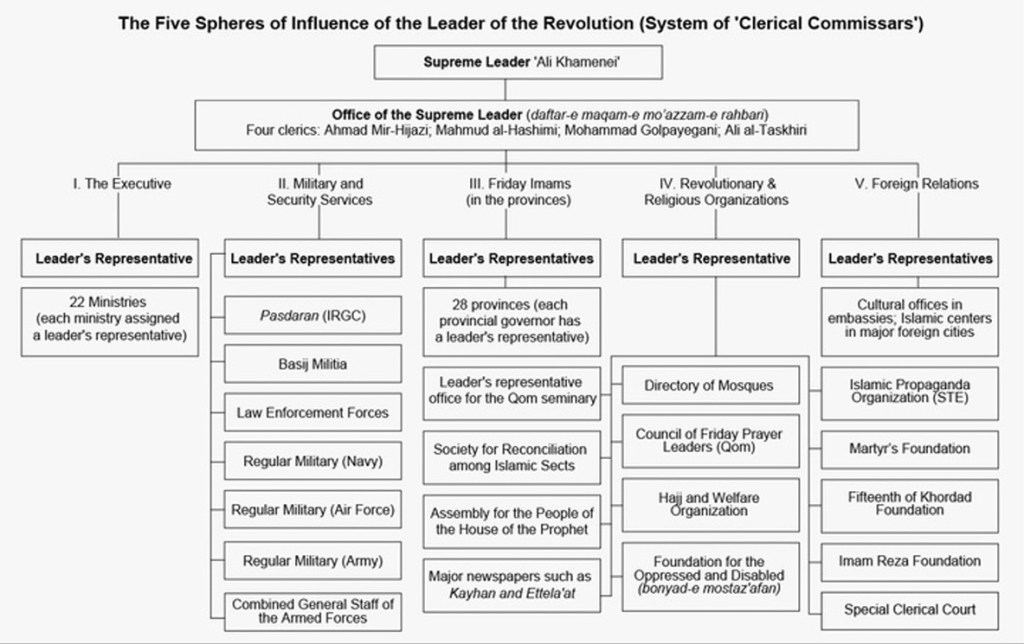
The accompanying graphic depicts how the supreme leader and the Bayt are organized in relation to each other. Other than the outer ring labeled “State Bureaucracy,” which are the public-facing official government agencies, everything else is part of the Bayt, which has no official designation. Since the IRGC functions as an elite military institution, and its headcount fluctuates from new recruits and departing guardsmen, only the officer corps is considered to be members of Bayt.
Khamenei and his hardline Bayt shadow government knew that over the ensuing decades, their infamous agenda would be on every western nation’s radar, especially the United States and Israel. Khamenei’s regime expected Iran would be attacked eventually, and it has.
Expecting an attack in the future, Khamenei’s Bayt began creating a religious, political and paramilitary (IRGC) infrastructure that could withstand a sustained, massive attack. A western military offensive, like Operation Epic Fury, might wipe out the visible signs of public and military infrastructure, but the shadowy Bayt would still be fully functional.
This “next-up-to-bat” dogma can readily be seen after Ali Khamenei’s death on the first day of bombing, including dozens and dozens of other regime officials. Only a week later, the remaining senior Bayt leaders met to vote-in the next supreme leader. The Israeli Mossad’s covert operatives identified the location of the selection conference; it was subsequently bombed, killing all of the attendees. Undaunted by the loss of so many senior leaders for the second time in a week, the remaining Bayt officials met, yet again, in an undisclosed location and chose Khamenei’s son, Mojtaba, as the new supreme leader.
Subsequent to Mojtaba’s ascension, he has not been seen in public. Regime experts have opined about his absence, citing three plausible reasons: 1.) Out of an abundance of caution, his security detail has counseled him to remain in hiding for a while, or 2.) The known injuries he sustained during the attack on his father are serious enough that he is still recovering under a doctor’s care, and; 3.) Announcing Mojtaba’s promotion is a ruse to deflect from the fact that he’s actually dead. This dogged determination by the Bayt to soldier-on as the country crumbles around them, is a good example of unreasonable behavior from a western viewpoint.
Applying the reasonable man theory in the face of relentless bombing, the death of more than 100 senior Bayt and government leaders, and the potential unfolding humanitarian disaster of the civilian populace, the remaining group of Bayt leaders should cease hostilities and sue for peace. But, that would be the actions of a reasonable, rational leadership team; the Bayt is clearly not that.
As long as the Bayt remains in power, regardless of how many senior officials and civilians might become casualties, the Bayt has achieved its ruthless goal of Regime survival. They literally do not care about the death and destruction surrounding them.
What is Next?
Unless the Bayt has a change of heart, rather than retaining its unreasonable position instead, the bombing campaign will not stop. At some point, however, the only way that the U.S. and Israel can achieve their goals is to send in a special forces team to root out the remaining members of the Bayt.
The difficulty of finding and eliminating a high profile adversary can be seen in the Israeli Defense Force’s hunt for Yahya Al-Sinwar, the embedded Hamas commander in the Gaza Strip. As formidable a military force anywhere, it took the IDF two weeks short of a year to locate and eliminate Al-Sinwar. Imagine the effort needed to find senior Bayt leaders in a country that’s twice the size of Alaska! President Trump and Benjamin Netanyahu have some sobering decisions to make if the Bayt leadership remains unreasonable.
Remember: What seems to be unreasonable to America, and her regional Arabic and Israeli allies, is not unreasonable from the Bayt’s viewpoint.

A Tribute to the 13 Troops Who Lost Their Lives at Hamid Karzai International Airport During the Evacuation of Afghanistan on August 26, 2021. 🇺🇸🫡🙏🎖️
A.I.’s Impact on 60 million American Workers in jobs such as, office support, customer service/sales, food services, and light production, are susceptible to A.I. replacement. The necessary workforce retraining into other occupations will create a National Security risk over the next six years when the country is in a critical position of being pulled into a near-peer shooting war.
Systemic Attacks on President Trump
In June 2023 I Posted This Clip To Social Media. I Called Out The Many Types Of Personal Attacks On President Trump, Like: Hateful Rhetoric, Yellow Journalism, And Liberal Lawfare. Now We Can Add Attempted Assassination.
The Democrat’s 2024 “All or Nothing” Presidential Campaign
The Democrat’s 2024 “All or Nothing” Presidential Campaign
RNSK Vol 2, Edition 7
What Was it Like as an Army Helicopter Door Gunner in Vietnam?
Published July 20, 2022
In terms of all forms of air combat across all services in the Vietnam War, the most dangerous job was Army air crewman on a Bell UH-1 “Huey” helicopter flying the new, highly successful air assault missions.
The Korean War (1950-53) revealed some important facts about helicopters: 1.) They were essential to ground combat and needed some serious RDT&E money to take advantage of the potential, and; 2.) Airborne assaults using paratroopers were an essential asset, but limited in terms of putting a platoon or company-sized element on-target without scattering soldiers over a wide area. The right kind of helicopter could revolutionize airborne combat assaults. The Huey helicopter was the game-changing assault platform the Army needed. Now a target could be Air Assaulted with precision, and limited only by the number of Hueys available.
The UH-1 was the first Army helicopter to use a jet engine connected to a transmission that powered the main and tail rotors. It was faster, had more range and climbed faster, too. With hydraulic-assisted controls, pilots said it was like flying a luxury car! They carried a 4-man crew and were designed to carry a 9-man infantry squad. In Vietnam, however, the oppressive heat and humidity robbed all helicopters of a lot of lifting capacity, and limited them to 6 soldiers instead of 9.
The Huey was flown primarily in the basic transport (“slick”) configuration and some as modified gunships. Being a door gunner on a slick and a gunship were very different jobs. Each aircraft had a crew chief with a maintenance mechanic MOS. The crew chief was quasi-owner of the bird, and was charged with keeping it flying, as well as flying on her. Door gunners were not from an aviation MOS; just someone willing to fly, live dangerously, and learned to be a good shot firing from a moving platform. They helped the crew chief work on the chopper, too.
A Huey gunship was adapted to carry (most of the time) forward firing 7.62mm miniguns and 7-tube, 2.75″ folding-fin aerial rockets. Crew chiefs and gunners on Huey gunships were primarily aboard as weapons mechanics and spotters. The Huey gunships were already weight-limited and unable to carry anything other than the four crewmen, the weapons and extra ammo. If the bird ever touched down during combat, it was because it was forced to.
The “slick” version was the most plentiful variant where the flying crew chief and door gunner had M60, 7.62mm machine guns for use as directed by the aircraft commander. A good door gunner realized very early on, the best way to stay alive was to not only shoot well, but to meld as quickly as possible with the crew chief on a day-to-day basis. Since pilots were assigned to fly different aircraft all of the time, crew chiefs and door gunners had to learn to mold themselves into a 4-man team every time they flew with different pilots. This meant acting and doing things to keep everyone safe, the chopper flying and the guns shooting without having to be told. If you did these things on a regular basis as a crew chief & door gunner, the word got around, and pilots felt good to have you “watching their six.”
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
Steve Miller © 2022 – All Rights Reserved
RNSK Vol 2, Edition 6
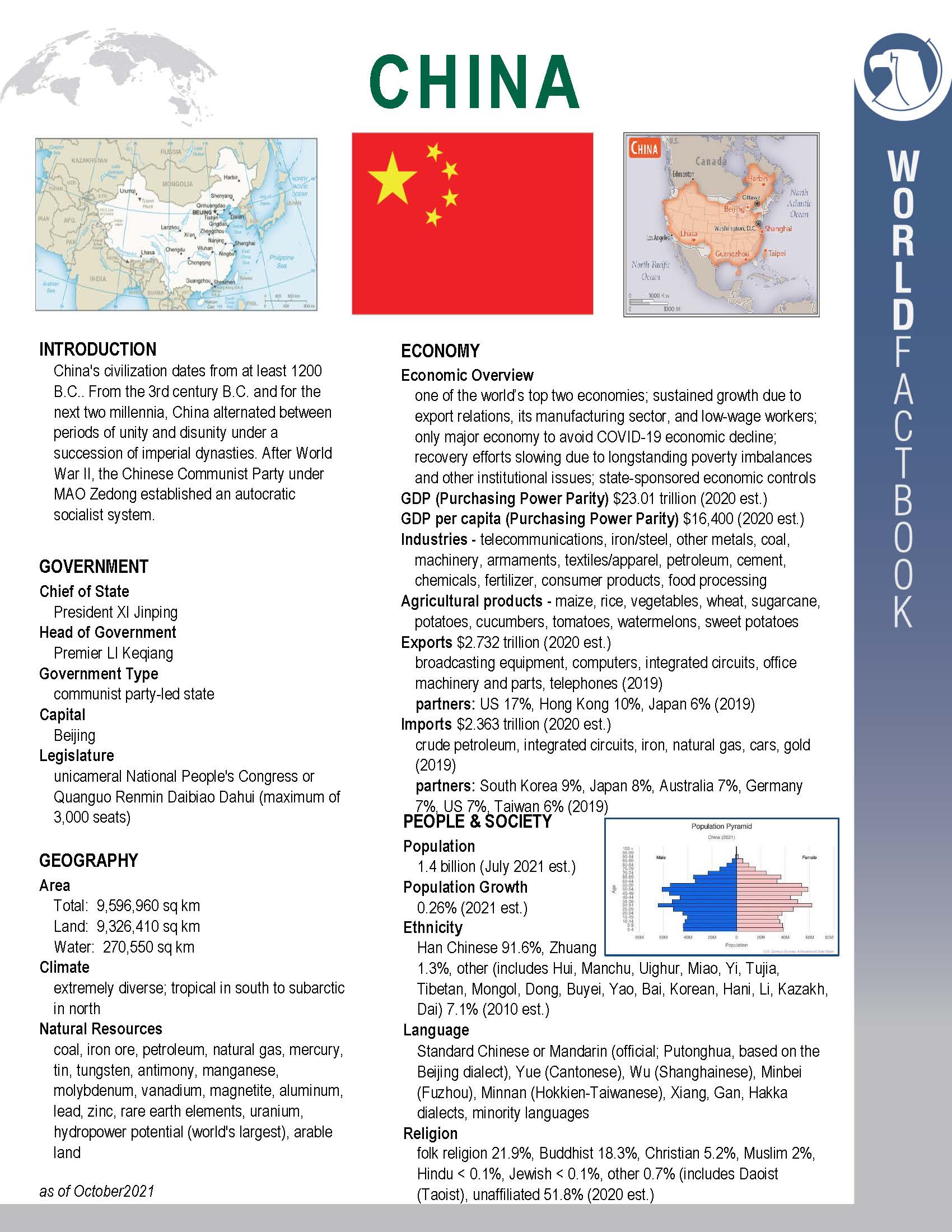
China: Getting to Know America’s Main Competitor
Published July 8, 2022

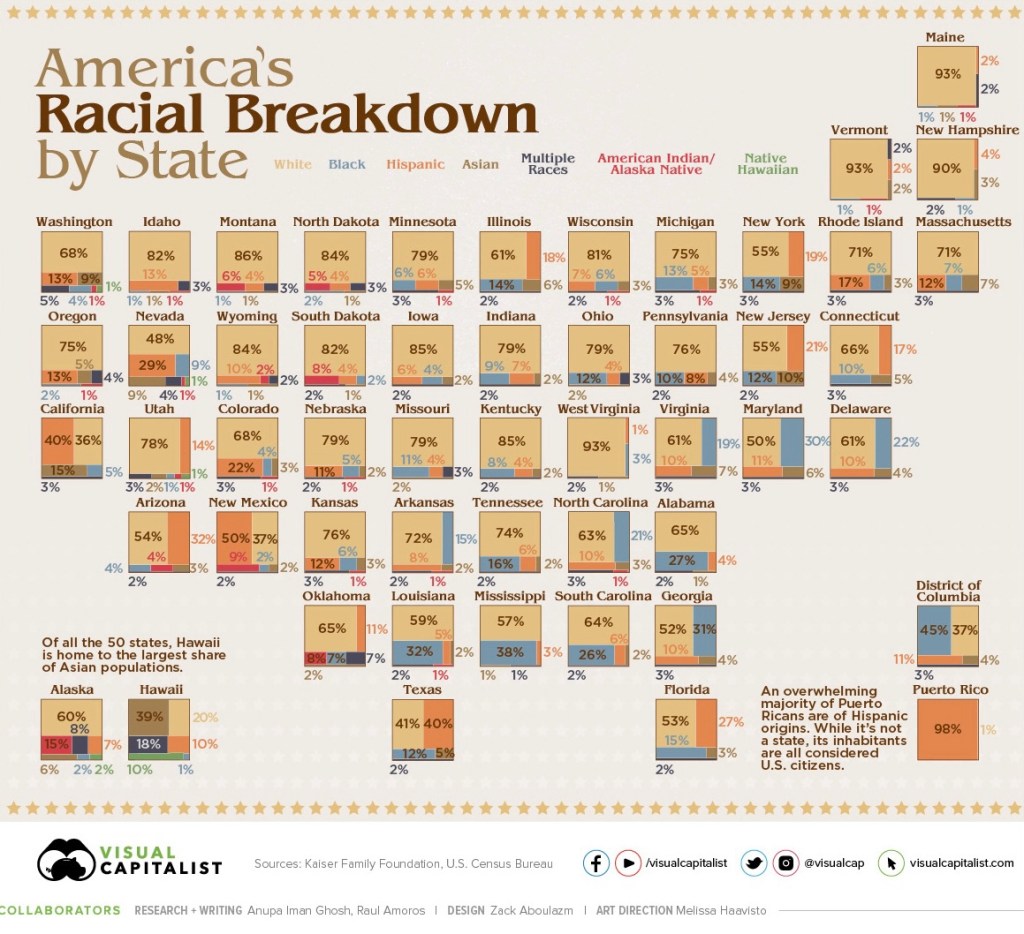
Americans need to start familiarizing themselves with China beyond knowing that they have a Great Wall, good food, and a high percentage of our consumer goods are made there! Friction between China and America will increase, and each country needs to prepare for the possibility of severing relations due to armed conflict. As the saying goes, “Know Your Enemy.” Obviously, no one wants a war between the two countries, but it would be foolish to not be prepared. Shown below is a basic primer about China.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
Steve Miller © 2022 – All Rights Reserved
RNSK Vol 2, Edition 5
UPDATE: American Weaponry & Gear Sent to Ukraine
Published July 8, 2022

In the 12 months preceding Russia’s unprovoked invasion of Ukraine on February 24th, the U.S. supplied approximately $700 million in military weaponry & gear. From the commencement of hostilities until July 1st, Ukraine has received $6.9 billion in military equipment, weaponry, and munitions from the U.S. The DoD announced on July 1st that an additional $820 million in military hardware was on its way to Ukraine.
For anyone familiar with the cost of military logistics, which encompasses the purchasing, transportation, storage, repair and inventorying of everything a military unit needs to function, it’s a massive, complex and costly endeavor. Numerous estimates have been reported on the annual cost of a soldier deployed to a war zone. It runs from $850,000-$1.4 mil. Granted, these are U.S. military costs, and Ukraine’s are likely half as much, if that. Regardless, you get the point that combat forces burn through an incredible amount of money to sustain the fight. By time U.S. and NATO equipment arrives in Ukraine, it’s quickly distributed. They don’t have the luxury of stockpiling.
Here’s a list of military gear that comprises the new $820 million package.
• 36,000 105mm artillery rounds;
• 126 Tactical Vehicles to tow 155mm Howitzers;
• 19 Tactical Vehicles to recover equipment;
• Eight High Mobility Artillery Rocket Systems and ammunition;
• Two National Advanced Surface-to-Air Missile Systems (NASAMS);
• 20 Mi-17 helicopters;
• 400+ Up-Armored Humvees;
• 200 M113 Armored Personnel Carriers;
• 10,000+ M203 grenade launchers, M4 Rifles and M9 Pistols;
• 59+ million rounds of small arms ammunition (including AK-47 ammo);
• 75,000 sets of body armor and helmets;
• 121 Phoenix Ghost Tactical Unmanned Aerial Systems;
• 1,000 AGR-20 70mm APKWS Laser-guided rocket systems;
• Puma Unmanned Aerial Systems;
• Six Unmanned Coastal Defense Vessels;
• 26 counter-artillery radars;
• Four counter-mortar radars;
• Four air surveillance radars;
• Two harpoon coastal defense systems;
• 18 coastal and riverine patrol boats;
• Explosive ordnance disposal protective gear;
• Medical supplies, including first-aid kits, and CBRNE protective gear;
• Electronic jamming equipment;
• Training, maintenance & sustainment
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
Steve Miller © 2022 – All Rights Reserved
RNSK Vol 2, Edition 4
A Famous Writer’s Most Profound Utterance About World War I
Published July 4, 2022
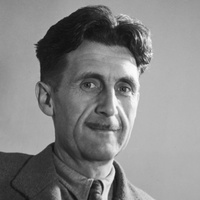
In May 1946, the famous English essayist, novelist & satirist, George Orwell (1903–1950), published an article in the short-lived British magazine “Polemic,” in which he analyzed the political, socioeconomic, and nationalistic single-mindedness of the four dominant state participants of World War I: England, Russia, Germany, and France. They all thought it would be a quick war. The concept of World War I being thought of as a quick war, became easy prey for journalists & authors during the War, and for the following 30+ years. Throughout this entire period, George Orwell grew into one of the most revered writers of the 20th Century.
It is fitting that an Orwellian comment about the folly of a quick war has been preserved. Orwell’s 1946 sobering quote has proven its enduring accuracy for decades.
Orwell said: “The quickest way of ending a war is to lose it.”
Read on to understand why he felt the way he did.
All wars are terrible, but World War I occupies a unique, but tragic place in history: It started based on the hubris of the major political powers noted above. There were no tyrannical despots involved; no hegemonic land-gobbling; no dastardly sneak attacks; no irreconcilable political squabbles in the pre-war years. Undoubtedly, Europe’s highly developed countries were compressed into a small area, and they could, at times, behave like a burlap sack full of cats! Compounding the problem that led to such horrific loss of life & destruction was the flawed military strategy on both sides that combined 20th Century weaponry with 19th Century ground combat tactics. An example of the mind-boggling statistics is the British Army’s losses at the 1916 Battle of the Somme, where they lost 60,000 soldiers on just the first day of battle. That’s equivalent to 12 army divisions.
Until June 28, 1914, everything was business as usual. Then in Sarajevo (modern-day capital of Bosnia-Herzegovina), a Bosnian dissident assassinated the heir to the Austro-Hungarian throne, Archduke Franz Ferdinand. High-level political wrangling ensued over the next 30 days over Austria-Hungary’s intent to “punish somebody” for the assassination. Due to a mish-mash of treaty alliances between the various countries, the hubris kicked-in when one country declared, “if you attack so & so, then we will attack you.” Then a third country said, “well, if you attack my friend, then I will come to his defense.” Meantime, everyone mobilized for war, and by July 28th no one would back down, with war being declared against each other: England, France & Russia, versus Germany, Austria-Hungary & the Ottoman Empire.
Quite literally, each country saw themselves as the embodiment of the right cause to fight for, and kept it that way for more than four years; no one was willing to back down. So self-assured were the major powers, that each thought the opposing armies would collapse in just a couple of months; in essence, it would be a quick war. Each belligerent saw themselves as victors, ensuring everyone would be home for the Christmas 1914. Instead of a “quick,” planned war of four months, the combatants got four years of unscripted warfare. Everyone was a loser in W.W. I.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
Steve Miller © 2022 – All Rights Reserved
RNSK Vol 2, Edition 3
How Knowledgeable Is The Average American About World Events & Trends?
Published July 3, 2022

In a nutshell: Americans are not as knowledgeable as they could, or should be.
Most people are aware of the American phrase,“Land of the Free.” Many Americans translate this freedom into “doing-their-own-thing,” meaning: “I am free to know as little as possible about anything happening at home or abroad.”
An amusing example of this philosophy can be found numerous times on You Tube. One of America’s best known comedians, Jay Leno, hosted a late night talk show for two decades. Leno frequently recorded a shtick during the day for use on the show later that night. He called it “Jay Walking.” Leno would go outside with a microphone and cameraman, and talk to passersby on the streets of Hollywood. One of his favorite questions was showing someone a picture of President Bush, and asking, “Who is this?” A high percentage of people had no clue who Bush was!
Here are some examples of legitimate questions asked by major polling organizations, such as, Gallup, the New York Times, and others. The question results are pretty scary!
1. 28% of those surveyed thought the United States and the Soviet Union fought each other in World War II; 44% did not know they were allies.
2. Three previous nuclear weapons treaties had already been completed by time the fourth nuclear treaty, SALT II, was inked. Right after SALT II was signed, American adults were polled about the two participants; 77% of the respondents did not know the treaty was between the Soviets and Americans.
3. Only 10 years after the Vietnam War was over – a war that claimed 58,000 American lives – less than 60% of American adults knew the U.S. fought on the side of South Vietnam.
These are just a few examples that demonstrate the frustrating apathy that is ever-present in American society. I am proud to be an American; but, it does not make the foregoing any easier to rationalize.
Even though globalization is spreading like wildfire, a large segment of the American population still lives their life in isolation, much like they did 100 years ago. The biggest difference back then versus now is: In 1920 a hard-scrabble life was common among Americans, but they still strongly believed in a participative democracy where the individual was subordinated to the whole.
Today’s America is more about redefining the meaning of democracy to focus on individualism, and the subordination of the whole.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
Steve Miller © 2022 – All Rights Reserved
RNSK Vol 2, Edition 2
United States Supreme Court Decision: U.S. v Abu Zubaydah Published March 3, 2022
An Important Decision In Protecting Classified National Security Information
Introduction
The Zubaydah case has significant National Security implications, and the Court ruled in favor of the United States. For most people, court cases can be pretty boring, and even more so at the Supreme Court level; unless, of course, you are fascinated by legal proceedings like me.
In the Zubaydah case, a common court procedure, “discovery,” became a critical issue that could have had a major effect on national security. In criminal cases, it sometimes becomes important for the prosecution or defense to prove or disprove the physical presence of a person involved in the case in order to establish a defendant’s guilt or innocence. However, a person’s physical presence at a certain location, or their whereabouts, is not always material to the case; this includes the location of someone when evidentiary information was obtained from them. For example, if a murderer confesses to a murder while in the back of the patrol car heading to jail, the fact that it occurred in the car makes no difference to its admissibility than if the defendant confessed to it in a police station interrogation room. In Zubaydah’s case, one of the attorneys-of-record decided to file a motion for discovery to determine Zubaydah’s physical presence at a certain location where his testimony/confession had been disclosed. This discovery motion is what stirred up national security concerns.
Background of the Case
Zubaydah is currently a detainee at the Guantanamo Bay Detention Facility. Zubaydah was a senior Al Qaeda lieutenant who was sought in connection with the World Trade Center Attack in September 2001. He was ultimately caught in 2002 and remanded to U.S. custody. During Zubaydah‘s detention in 2010, he filed a lawsuit against the USG, alleging that in 2002-2003 he was held by the CIA at a “black site” in Poland. His lawsuit complained that he was unlawfully detained at the black site, citing the Supreme Court decision that enhanced interrogation techniques were illegal, as well as, unlawful detention, which prejudiced his criminal arrest warrant for conspiracy in the 9-11 attacks, and therefore any information which may have been obtained from Zubaydah was inadmissible; ergo his case ought to be dismissed.
Zubaydah had/has multiple criminal charges pending, with some relying on the confession/testimony he alleged came from his black site detention. Although Zubaydah’s black site claim might get the charges dropped that relied on information obtained at the black site, it would not affect other pending charges that did not rely on that information. Sometimes a key factor in a criminal case is proving/disproving the defendant was/was not physically present at the location(s) where events of the case may have occurred. In the case of Zubaydah, the information he revealed at the alleged Polish black site had been confirmed by the USG as valid, but that was not as important as the alleged location where information was obtained.
U.S. District Court Activities
When the district court considered the defense’s discovery motion, which requested the CIA disclose the location where the defendant’s confession/testimony was obtained, the prosecutors declined to confirm/deny anything about a Polish black site, citing that CIA methods & trade craft are classified information that may harm U.S. national security if revealed. Prosecutors stated that it was common practice by the USG that when the public requested information, or asked for corroboration of certain information already in the public domain, which may or may not have classified national security implications, the USG may choose to reply that they cannot confirm or deny what was being asked for. Prosecutors further stated that there was no statute or case law that compelled the USG to declassify and disclose classified national security information based on a formal or informal request, regardless if the requestor alleges the information is already public knowledge. The prosecution moved to dismiss the discovery motion. The District Court judge concurred with the CIA, dismissing Zubaydah’s discovery motion, as well as dismissing the defense’s lawsuit against the CIA. None of these proceedings had any immediate affect one way or the other on pending criminal charges against Zubaydah, and other defendants, that stemmed from the alleged Zubaydah black site interrogation.
U.S. Court of Appeals Activities
Zubaydah’s attorneys appealed the lower court decision to dismiss the discovery motion, and the lawsuit, to the 9th Circuit Court of Appeals. Zubaydah’s attorney’s submitted that once classified information is found in the public domain, which was alleged to be the case about the black site’s existence, it was no longer sensitive, national security-classified information. In layman’s terms, it was like “the-cat-was-already-out-of-the-bag,” so what’s the big deal? The Appeals Court agreed with the defendant, and reversed the District Court’s ruling, agreeing that once the information was in the public domain, it was moot to retain a national security classification. Reversing the lower court’s dismissal of the discovery motion, and lawsuit, meant the USG could be compelled to acknowledge the black site’s existence in Court, and any details about it. The case was remanded back to the District Court, where Zubaydah’s attorneys would compel the CIA to reveal the black site’s existence, and therefore move to dismiss criminal case(s) based on the Supreme Court’s prior ruling that black site detention locations and enhanced interrogation techniques were unconstitutional.
U.S. Supreme Court Activities
Before the District Court judge could rule on reversing the dismissal of the discovery motion, and lawsuit, based on Appeals Court guidance, CIA lawyers sought an injunction from the Supreme Court until they could rule on the merits of the motion-to-dismiss. The injunction was granted, allowing time for the case to be heard by The Supreme Court. After the prosecution and defense argued their cases in front of the Court, the Court issued a ruling in favor of the CIA. The Court opinion noted that it has been standard USG practice that if any sort of classified information has been disclosed to the public, the USG is not required to confirm or deny anything about the alleged classified information, since it was classified by the USG in the first place.
Basically, just because alleged classified information has been leaked to the public, the U.S. Government is not required to comment or corroborate the leaked information. This would be a kin to releasing photos to the public of a man standing on the sidewalk near a bank that was being robbed, with the photo clearly showing he was looking right at the robbers as they exited the bank to leave in their getaway car. Speculation was rampant on social media that the man in the photo was a well-known baseball player, but the picture was grainy, and no one was 100% positive it was him. If a discovery motion was filed by the prosecution to compel the baseball player to admit it was him in the picture, and thereby subpoena him to testify against the robbers, but the player is not being charged or investigated for wrongdoing, there’s no statute or case law that says he is required to confirm his identity.
The concept here that applies to national security information is that if it is leaked to the public, the USG cannot be compelled to publicly acknowledge the veracity of the information, nor whether it carries a national security classification, if any. Had the Supreme Court allowed that any alleged USG privileged information that was compromised to the public, could compel the USG to confirm or deny it, if so requested, could cause unintended harm to others. This would mean that such information as might appear on Wikileaks, for example, anyone could submit a formal request to USG compelling them to disclose the veracity of the information.
Aftermath of the Supreme Court Ruling
In the Zubaydah case, the defense attorneys were quite shrewd. By filing a discovery motion seeking to compel the USG to confirm or deny the site, whatever the outcome, the cases stemming from the information obtained at the black site would end up being dismissed. If the CIA confirmed the black site’s existence and the information obtained there, those cases would be dismissed, BUT more importantly, it would have damaged the Polish government in the court of public opinion for allowing the black site operation, as well as, destroy any trust between the two governments. Alternatively, if the CIA denied the black site’s existence, they would be committing perjury, which has no statute of limitations. Poland’s reputation would remain intact, and Zubaydah would likely have been convicted of the crimes stemming from the black site-obtained information. The third option, which was allowed by the Supreme Court, gave the CIA the ability to use the standard reply in these situations – that the information could not be confirmed or denied. This kept Poland’s reputation intact, and did not require the USG to corroborate classified information in the public domain. Unfortunately, the third option meant the District Court’s dismissal of the defense’s discovery motion might create doubt as to the validity of the information if it were utilized in a jury trial. The defense would show the jury that the prosecution could not testify as to where or how the incriminating information was obtained, thereby casting suspicion on the veracity of it. The jury would learn the USG was hiding something, and be unlikely to convict someone using evidence that may have been obtained illegally. So, rather than chase down that rabbit hole, the prosecution had no choice but to concur with the judge’s ruling to dismiss the case(s) using the black site information. Zubaydah still had many other charges pending based on other evidence, but the defense attorney’s very shrewdly got rid of a sizable chunk of the court cases against Zubaydah. Other defendants implicated in Zubaydah’s black site testimony also had some charges dropped.
The moral to this story is that a democratic form of government has a lot more plusses than minuses. In order to have the benefit of all of the favorable aspects of living in the United States, there are going to be times that you have no choice but to accept the bad. No one really doubted Zubaydah’s guilt; he would be convicted on other charges stemming from different information sources. But to get a conviction (a good outcome of democracy) on Zubaydah’s black site confession, it would have required representatives of the U.S. Government to lie under oath (a bad choice), which is not how a democracy works. Zubaydah and his attorneys relied on the fact America’s democratic-based legal system would get him off-the-hook.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com

RNSK Vol I, Edition 7
August 9, 2021
A Tale of Two “Skits”
It has been a wild ride in America since March 2020 when the COVID-19 pandemic hit. No one I’ve spoken to can recall a time when there was so much unrest in society. Even all the unrest in the 1960s related to civil rights, the Cold War, and the Vietnam War, pale in comparison to 2020. In 2020-2021, we’ve had police brutality, rioting, extensive destruction of government & personal property, multiple crime waves, subversion, racism, inner-city murders on an unprecedented scale, assault & battery in broad daylight, and hate crimes of every type. In fact, who would have thought that one of the most security-conscious environments, passenger airliners, would see so many on-board fights & unruly passengers? It was a chaotic year that surprised and disturbed most of us. I saw things that I never dreamed I would see in my lifetime.
Back in 1970 I was a junior in high school. I had always been interested in the behind-the-scenes stuff that it took to make movies & T.V. shows. So, I took an elective that year in school called “Technical Theater.” We learned all about building sets, lighting, filming, script supervision, etc. The Technical Theater class served as the production crew for any school plays or concerts.
One day we were gathered in the school’s theater waiting for a beginner’s acting class to finish before we could start some set construction. The beginners were doing improvised, satirical skits, so we casually watched the last two.
In the first skit the teens all lined-up facing the audience. When the teacher called, “action,” the students all started acting like little kids who were standing in a line. They fidgeted, whispered to each other, and jabbed elbows into their neighbor. Typical little kids with ants-in-their-pants. One kid took a step forward and said, “the first grade class of Mary Louise Phillips Elementary School will now say the Pledge of Allegiance to the Flag.” The kid got back in line and told the others, “right hand over your heart, ready…begin…”
As they started to say the pledge, some elbowing got out of hand and two boys shoved each other. Finally, one of them was knocked to the ground, and the other kid kicked him. At this point the Pledge stopped, and all of the kids in the line ran up to the kid on the ground. Rather than helping him up, they jumped-in with the bully who started it, and pretended to give this kid a class “A” beat-down! When they were done, they got back in line. The kid on the ground was now “dead.” After the kids were lined-up again, they cleared their throats and said “…with liberty and justice for all.”
It was supposed to be satirical and we all chuckled mildly. At the time I thought, “well, that was pretty far-fetched…ha!…like that would ever happen in real life.”
The second skit had the students laying on the stage as if they were relaxing under some trees in the park. One kid declared, “it’s a nice day.” Another said rather laconically, “yep, it’s a nice day.” A third kid apparently thought the second kid was being mockingly sarcastic, so he ran over to the second one and loudly yelled in his face, IT’S A NICE DAY!!!” The rest of the kids started chanting, “it’s a nice day…it’s a nice day…it’s a nice day,” as they closed-in on the second kid. The second kid tried to leave, but the group shoved him to the ground and beat the living daylights out of him! Once the second kid acted like he was knocked-out, the others laid down to relax on the grass again. The very first kid who made the nice day comment piped-up and said, “you know, it REALLY is a nice day.”
Hmmm…So, what is the tale of the two skits? In a Vietnam Era, American high school, I saw two skits with ridiculously weird outcomes. There’s no way that either scenario could occur in real life, right? A group of ordinary people could never be so unbalanced that they would assault another person for no apparent reason. I held this belief over the past 50 years; there was NO tale to tell about the two skits…they were just part of a scriptwriter’s imagination.
Then 2020 came around and changed how I felt about the Tale of the Two Skits. The screwy circumstances in the skits were no longer implausible. We are in an era of contempt by many toward our national symbols…The Pledge of Allegiance, The National Anthem, and the U.S. Flag. And the contempt for these symbols has now transcended the average citizen to public institutions and elected officials. What used to be symbols of unity, are now lightning rods of divisiveness.
What about the kids in the first skit symbolizing what is normally a benign gathering…saying the Pledge of Allegiance? Kids and adults will both act out sometimes, and the level of behavior used to be more commensurate to the situation. We were taught that if you need to argue, do it behind closed doors, or take it outside if it is really heated. Nowadays people seem determined that whatever might occur between two people is not taken off-line; it is going down right where they stand in the grocery line, in the bleachers at a ball game, or a local park while kids play on the nearby jungle gym. What used to be two people discussing differing viewpoints, is now an open disagreement. An open disagreement is now a serious argument. A serious argument is now a shoving match. A shoving match is now physical assault. Physical assault is now battery with the intent to do serious physical harm. The intent to do serious physical harm has now escalated into the use of weapons for defensive self-protection. And finally, defensively brandishing a weapon to break-free from a fight is now using a weapon to permanently stop an altercation with someone, by killing them.
In the second skit, the teenager who took exception to what the second kid said, did so by simply reacting and immediately passing judgment. No wisdom or discernment was applied…just react and judge. American society is experiencing an unprecedented wave of public reaction & judgment. Wisdom, discernment and cooler heads prevailing, seems lacking in 2020 America.
In today’s world, the Tale of Two Skits from 50 years ago would still be considered satirical. But, do the two scenarios, or something similar, still seem like an absurd piece of fiction in 2021? The underlying human behavior (not actual school kids or teens in a park) and the outcomes seem quite plausible to me. If the American Dream could be compared to a sunny day, I would say the sun is still there…it just does not rise as high as it used to.
I feel certain that someday American society will exceed the fiction of The Tale of Two Skits…sigh…
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com

RNSK Vol I, Edition 6
September 29, 2020
America’s Strategic Reserves-Part I
 photo courtesy of the Defense Logistics Agency
photo courtesy of the Defense Logistics Agency
Introduction
During the recent COVID-19 Pandemic, there was much discussion about the materials, products and equipment contained in the Strategic National Stockpile (SNS). People wondered what was in the SNS, who decided what to put into it, how much is stored in it, where the SNS is located, the policies & procedures for replenishing it, and the logistics for accessing the stockpile for use. It seems appropriate at this time to educate everyone about America’s strategic reserves. The fact is: there is more than one type of reserve stockpile, with different governing statutes for each one of them. These four reserves are in chronological order, with the longest tenured reserve listed first:
- The National Defense Stockpile (DNS)
- The Strategic Petroleum Reserve (SPR)
- The Strategic National Stockpile (SNS)
- The National Veterinary Stockpile (NVS)
The Strategic National Stockpile is the program that has been so heavily covered by the news media throughout the COVID-19 Pandemic. For purposes of our discussion here, the National Defense Stockpile will be discussed first. The NDS came into existence 35 years before the Strategic Petroleum Reserve; much of the institutional learning, best practices, and the do’s & don’ts of managing such a huge undertaking, became the blueprint for the three follow-on programs. The DNS will be discussed first to set the table. Subsequent editions of the RNSK will cover each stockpile type separately.
The National Defense Stockpile (NDS)
The NDS first came into being in 1939 when the U.S. Congress passed the Strategic and Critical Materials Stock Piling Act. President Franklin D. Roosevelt pressed for the law, but, it was no easy feat. Starting in 1934, and continuing through 1939, Congress passed a series of increasingly stringent neutrality laws. The laws were intended to minimize the chance of America getting dragged into another foreign war, such as World War I. The possibility of another large scale conflict was a legitimate concern throughout the 1930s. When the first neutrality law was passed in 1934, Hitler and the Nazis had been in power over a year, and Japan had invaded and occupied the northern region of China, known as Manchuria, in 1931. When President Roosevelt championed the Stock Piling Act, many members of Congress thought it was just another indication of the country heading to war. Fortunately, there were enough Senators and Representatives who recognized the need to stockpile critical resources, regardless of any future war, and got the stockpile law passed.
The NDS statutes are contained in Title 50, Chapter 98, United States Code, and have been amended from time-to-time. The law provides for the acquisition and retention of certain strategic and critical materials to reduce and mitigate U.S. dependence on foreign sources or single points of failure in the strategic materials supply chain in times of national emergency. These materials are purchased and stored, forming what is known as the National Defense Stockpile.
The NDS Manager is the Secretary of Defense, however, he does not manage the stockpile directly. The NDS falls under the Assistant Secretary of Defense for Sustainment. The actual managing organization is the Defense Logistics Agency, led by a three-star Admiral or General, in Ft. Belvoir, VA. A civil service manager runs the Strategic Materials Directorate, also at Ft. Belvoir. In addition to the noted Defense Department organization just discussed, Title 50, Chapter 98, USC, also assigns certain limited duties to the Interior Department and the Agriculture Department. Although the Defense Department manages the actual stockpile operations, and is charged with acquiring the designated strategic materials listed in the statutes, the other two executive departments have NDS duties related to the research, development and contingency plans of domestic sources of supply. For example, the Interior Department’s U.S. Geological Survey is responsible for strategic preparedness in a national emergency for various NDS metals and minerals that can be exploited domestically. Similarly, the Agriculture Department utilizes its Agricultural Research Service and U.S. Forest Service to conduct R&D and contingency plans to capitalize on agricultural products that could be diverted for alternative uses to supplement possible NDS shortfalls in a national emergency.
The List of NDS Strategic Materials
The NDS statutes currently list 64 strategic materials in four major categories: Compounds, Metals, Non-Metals, and Rare Earth Elements. As a point of clarification, Rare Earth Elements are often mistaken for precious metals, such as gold, silver and platinum, assuming a high value metal is synonymous with the term “Rare.” In actuality, “Rare Earth” refers to the fact that these elements are “rarely” found in nature in their pure form; they are mixed-in with other kinds of ore, making the mining and pure element extraction process difficult and expensive. The list of materials below are managed directly by the NDS at their several depot locations.
| Aluminum (Al/13) | Graphite/Carbon (C/6) | Quartz Crystal |
| Antimony (Sb/51) | Hafnium (Hf/72) | Rhenium (Re/75) |
| Arsenic (As/33) | Holmium (Ho/67) | Samarium (Sm/62) |
| Barium Sulfate (BaSO4) | Indium (In/49) | Scandium (Sc/21) |
| Beryllium (Be/4) | Iridium (Ir/77) | Selenium (Se/34) |
| Bismuth (Bi/83) | Lanthanum (La/57) | Silicon (Si/14) |
| Boron (B/5) | Lead (Pb/82) | Strontium (Sr/38) |
| Cadmium (Cd/48) | Lithium (Li/3) | Tantalum (Ta/73) |
| Calcium Fluoride (CaF2) | Lutetium (Lu/71) | Tellurium (Te/52) |
| Cerium (Ce/58) | Magnesium (Mg/12) | Terbium (Tb/65) |
| Chromium (Cr/24) | Manganese (Mn/25) | Thulium (Tm/69) |
| Cobalt (Co/27) | Mercury (Hg/80) | Tin (Sn/50) |
| Copper (Cu/29) | Molybdenum (Mo/42) | Titanium (Ti/22) |
| Dysprosium (Dy/66) | Neodymium (Nd/60) | Tungsten (W/74) |
| Erbium (Er/68) | Nickel (Ni/28) | Vanadium (V/23) |
| Europium (Eu/63) | Niobium (Nb/41) | Ytterbium (Yb/70) |
| Gadolinium (Gd/64) | Palladium (Pd/46) | Yttrium (Y/39) |
| Gallium (Ga/31) | Platinum (Pt/78) | Zinc (Zn/30) |
| Germanium (Ge/32) | Praseodymium (Pr/59) | Zirconium (Zr/40) |
The following seven materials are managed directly by the Interior Department on behalf of the NDS.
| Cesium (Cs/55) |
| Helium (He/2) |
| Natural Rubber |
| Potash (potassium compounds) |
| Rubidium (Rb/37) |
| Silver (Ag/47) |
| Uranium (U/92) |
The NDS Management Process & Locations
NDS materials are stored at 6 locations throughout the U.S. and have a current market value of approximately $1.1 billion. These material depots are located on U.S. Government property managed by the Defense Logistics Agency, and are used for many other DoD programs, including equipment repair & storage, weapons & munitions magazines, surplus equipment disposal, and others. Although the NDS does not publicly disclose how much material they have on-hand, or what is stored in each location, there is no need to make their whereabouts classified information. The NDS depots are already located on heavily guarded military installations, and even if a major theft were to occur, the items in storage are industrial grade materials that would be extremely difficult to sell on the black market without getting caught. All six depots are extremely large, multi-building installations that are located well inside the country’s international boundaries. An enemy attack by air or ground forces would be a high risk, one-way mission by those involved. Since individual NDS materials are each stored at multiple locations, it would be nearly impossible to launch six massive raids in a coordinated, simultaneous attack. About the only way an adversary could deliver a knockout blow to the NDS would be by nuclear weapons at all six depots at once. It would be no easy task.
Locations
- Hammond, IN
- Hawthorne, NV
- Lordstown, OH
- Pt. Pleasant, WV
- Scotia, NY
- Wenden, AZ
Historical Perspective of the National Defense Stockpile
The average person, American or otherwise, has only a cursory understanding of the depths and implications of a worldwide war, such as World War I from 1914-1918, and World War II from 1939-1945. Wars conducted since 1945 have all been regionalized, and primarily affected just the engaged belligerent nations. In terms of economic impact, human sacrifice and other privations of war, the most seriously affected are the nations where the heaviest combat operations occurred. For belligerents in a regional conflict who had no actual combat operations on their own soil, such as the United States during the Vietnam War, daily life at home was virtually unaffected for 95% of the population.
Global warfare, however, is much different. It is not just a clash of opposing military forces, but, creates hardships and sacrifice in all walks of life. As the name implies, global warfare has few geographic, economic, or human boundaries…all aspects of global life are “fair game.”
In most wars, global or regional, they begin with a clash of military forces from opposing sides. Naval warships are attacked and possibly sunk; military aircraft bomb adversary forces and installations; adversaries shoot down each other’s planes, and adversary armies engage each other. These force-on-force confrontations, known as tactical warfare, are what the average person thinks of in terms of what war is.
But, when wars spread into other countries, become protracted, and consume ever greater amounts of manpower and materials, tactical warfare becomes less able to bring victory to one adversary versus another. At this point both sides continue to engage in tactical warfare to essentially keep the pressure on, but, now strategic warfare enters the picture. The essence of strategic warfare is to disable an adversary’s means and will to wage war. This can take many forms, including: information warfare, espionage, sabotage, clandestine intelligence operations, infrastructure destruction, and commerce or trade warfare. The NDS’s primary role is to deter or mitigate an adversary’s efforts to disrupt commerce by denying the U.S.’s ability to obtain the raw materials necessary to wage war.
In both world wars, after the opening rounds of force-on-force combat engagements on the sea, in the air, and on the ground, the major combatants began commerce warfare. This was most evident in the Atlantic Ocean where submarines of the German Kreigsmarine waged unrestricted warfare on all Allied merchant shipping. Submarines of the American Navy waged unrestricted submarine warfare in the Pacific Ocean on all Japanese merchant shipping. By the end of the war, American submarines had destroyed or sunk 75% of all Japanese merchant vessels. This choked-off Japan’s ability to obtain oil, rubber, and many critical metals needed to produce aircraft, ships and weapons. The NDS program is designed to counter the effects of strategic commerce warfare stemming from a major military conflict, or an embargo imposed by an unfriendly nation. The United States uses embargoes and sanctions against certain countries quite effectively. This is especially true when a country does not have a robust strategic national stockpile program that covers multiple categories of raw material, oil, equipment, medical supplies, etc.
Implications of Commerce Warfare, Embargoes and Sanctions in 2020
In today’s terms, the United Nations Conference on Trade and Development (UNCTAD) estimates that roughly 80 percent of all global trade – by rail, truck, ship and plane – is transported by sea. Of the total global trade volume by all means, 34% of it passes through the South China Sea by ship!

| Country | % Share of World GDP | Trade Value through South China Sea (USD billions) | South China Sea Trade As % of All Trade in Goods |
| United States | 24.5 | 208 | 5.72 |
| China | 14.8 | 1470 | 39.5 |
The United States and China represent the two largest shares of the world’s total Gross Domestic Product (GDP). Of the top 10 countries with goods transiting the South China Sea, nearly 40% of Chinese goods transported by all means moves by ship through the South China Sea. By comparison, India and Brazil at 30% & 23%, respectively, are the next highest behind China. Of the other top 10 South China Sea users, The United States is ninth, and Canada is tenth at less than 3%. The vast majority of ocean trade bound for the United States heads directly into the Pacific Ocean bound for Seattle/Tacoma, San Francisco Bay or Los Angeles/Long Beach.
It is quite clear that the South China Sea is a critical trade route for China. Most traffic takes the shortest route through the Malacca Straight between Indonesia and Malaysia. Alternative routes are not only more expensive and time consuming, but, also pose a greater security risk for China. This is why China has spent the past 15+ years claiming islands and building military bases in the South China Sea. These moves have been heavily disputed in international court by Vietnam, The Philippines and Taiwan. Thus far, court cases have ruled against China, but, they refuse to recognize these decisions. The United States’ strategic partnering with The Philippines and Vietnam has taken on greater importance in the past decade. The U.S. Navy continues to sail its ships through the South China Sea based on freedom of navigation under international maritime law. China heavily disputes America’s presence. Strategic military analysts have stated for nearly 20 years that if a large scale war was to break out somewhere, it would likely be in the South China Sea. This situation has led to China’s massive shipbuilding program, putting its Navy on a par with the U.S. Navy in terms of the number of vessels.
Analyzing the Most Critical NDS Materials
Whereas, China’s greatest strategic concern is the risk of moving materials through the South China Sea, America’s risks are more diverse. Some of the risk stems from large coastlines on three major oceans, and many critical NDS materials are not easily sourced in the U.S. The NDS sources a number of critical materials from countries such as China, and some of the less stable third-world countries in Asia and Africa. Any of these states could experience a supply chain disruption due to political instability, military actions, or disagreements over trade. In most cases the NDS has sourcing alternatives in-place for the more risky material acquisitions. The following list of materials are some of the most challenging in terms of acquiring sufficient quantities for emergency stockpile use.
- Barium Sulfate (BaSO4) More than 90% of this compound sold in the US is used as a weighting agent in fluids used in the drilling of oil and natural gas wells. Substitute materials have thus far not been commercially viable. Although Barium Sulfate resources exist in the U.S., they have never been commercially developed. The greatest risk with this material is that everything is imported from four major sources, with China being number one at 58%, and then India, 17%; Morocco, 12%; Mexico, 11%.
-
Cadmium (Cd/48) Cadmium is generally recovered from zinc ores, and most of the world’s primary cadmium metal is produced in Asia, and leading global producers are China, the Republic of Korea, and Japan. The U.S. has negligible Cadmium resources and imports come from: China, 25%; Australia, 22%; Canada, 21%; Peru, 10%; and other, 22%.
-
Cesium (Cs/55) The metal ignites spontaneously in the presence of air and reacts explosively in water. Because of this reactivity, cesium is classed as a hazardous material and must be stored and transported in isolation from possible reactants. The U.S. only uses a 6,000-7,000 lbs of cesium per year. There are no domestic sources of cesium, so everything is imported. The NDS does not publish cesium import statistics, but, Canada is believed to be the primary supplier. Cesium is an uncommon element that can be mined in only a few places in the world. Canada accounts for more than two-thirds of world reserves.
-
Gallium (Ga/31) Gallium is used primarily in integrated circuits (cell phones, especially smart phones, wireless internet); optoelectronic devices (laser diodes, LEDs, photo-detectors, and solar cells). Gallium-based ICs are used in many defense-related electronics, and no effective substitutes exist for Gallium in these applications. It is not produced in the U.S., and demand is satisfied solely by imports from China, 50%; United Kingdom, 18%; Germany, 10%; Ukraine, 9%; and several lesser sources. China’s Gallium resources, and the U.S.’s lack of resources, poses a national security risk to the United States.
-
Tungsten (W/74) Tungsten is a heavy, hard metal that is stronger than any other known element. It is very expensive, and due to its mechanical properties it is used in wear-resistant alloys, in nickel super-alloys for high-temperature sections of jet engines, armor penetrating projectiles, aircraft weights and counterweights, and small arms ammunition. China ranks first in the world in terms of tungsten resources and reserves and has some of the largest deposits. Canada, Kazakhstan, Russia, and the U.S. also have significant tungsten resources. The U.S., however, has not had an operating tungsten mine since 2015. All tungsten is imported from the following countries: China, 31%; Bolivia, 10%; Germany, 9%; Spain, 6%; and all others, 44%.
-
Arsenic (As/33) When the average person hears the word “arsenic,” their first thought is, “oh, that’s a poison.” It is a fact that arsenic is used in pesticides and herbicides. In terms of being a critical NDS material, however, arsenic has a very important usage in the production of Gallium-Arsenide (GaAs) semiconductors for solar cells, space research, and telecommunications. It is also used for specialty optical products, and in electronic components for short-wave infrared technology. Many defense-related electronic products would be hard pressed to meet their performance specifications without GaAs components. Arsenic is rarely found as a pure element, and is often found in copper, gold and lead deposits. When these metals are refined into their purest form, the by-product is set aside for further extraction of any remaining elements, like arsenic, if economically feasible. The easiest ore to recover arsenic from is arsenic trioxide, but, it has only been found in China and Morocco. Morocco does not have the ability to refine the material, so, they sell it for export. Several other countries have arsenic refining capability. China, on the other hand, has an extensive arsenic trioxide refining capacity, and accounts for 93% of refined arsenic sold worldwide. This poses a national security threat to the U.S. because the other countries that can refine arsenic have only a small fraction of China’s processing capacity. The US is 100% import reliant for its arsenic needs.
-
Germanium (Ge/32) Germanium is mainly a byproduct of zinc ore processing. Germanium is a semiconductor, with electrical properties between those of a metal and an insulator. Other than electronic components, germanium is used in telecommunication fiber optics, lenses for infrared (IR) devices in military applications, and solar cells. Fiber-optic cable manufacturing accounts for about one-third of global germanium consumption. Although China remains the leading global producer of germanium, the U.S. has substantial reserves of recoverable germanium contained in zinc deposits in Alaska and Tennessee. The U.S. imports refined germanium from the following countries: China, 59%; Belgium, 22%; Germany, 9%; Russia, 7%; and others, 3%.
-
Rare earth elements – Cerium (Ce/58), Dysprosium (Dy/66), Erbium (Er/68), Europium (Eu/63), Gadolinium (Gd/64), Holmium (Ho/67), Lanthanum (La/57), Lutetium (Lu/71), Neodymium (Nd/60), Praseodymium (Pr/59), Scandium (Sc/21), Terbium (Tb/65), Thulium (Tm/69), Ytterbium (Yb/70), and Yttrium (Y/39). Rare earths are relatively abundant in the Earth’s crust, but minable concentrations are less common than for most other ores. Nearly all countries have rare earth elements, but, because extraction and processing costs are high, most countries do not invest their time or money to develop the industry. China accounts for 80% rare earth materials mined and sold worldwide. Other producers include: Estonia, Japan, Malaysia, Brazil, Australia, and India. The U.S. has not made much effort to mine and produce rare earth materials on its own; they are 100% reliant on imports. The estimated distribution of rare earths by end use are as follows: catalysts, 75%; metallurgical applications and alloys, 5%; ceramics and glass, 5%; polishing, 5%; and others, 10%.
Wrapping It Up
The Congress of the United States has authorized the NDS to sell commodities that are excess to Department of Defense needs. Sales of excess NDS materials produce revenue for the Treasury General Fund and a variety of defense programs such as the Foreign Military Sales program, military personnel benefits, and the buy-back of broadband frequencies for military use. The sales revenue also funds NDS operations to make it a self-sustaining organization. Because of the broad portfolio of materials held by the NDS, there is no private sector company in the world that sells this wide range of commodities and materials.
Approximately 35% of the 64 types of material held by the NDS are traded on the open commodities markets. Examples include copper traded on the London Metals Exchange, platinum traded on the New York Mercantile Exchange, and rubber on the Tokyo Commodities Exchange. Because the NDS purchases these traded commodities in such high volume, they buy them directly from the exchanges, and not from individual private sector companies or sellers. This means NDS staff members involved in these transactions have to hold commodities broker licenses.
Since the NDS is a U.S. Government agency, everything they buy and sell is done via announced solicitations. This allows qualified contractors to submit sealed bids for the purchase of commodities from the NDS. In October 2019, for example, the NDS announced that at various dates to be determined in FY2020, there may be potential sales of the following materials from NDS inventory: Beryllium, Chromium, Germanium Scrap, Manganese, Nickel Alloys, Platinum, Iridium, Tantalum Carbide Powder, Titanium Based Alloys, Tungsten Metal Powder, and Zinc. The October 2019 announcement also indicated the maximum amount the NDS planned to sell of each material.
The NDS also announces every October their potential fiscal year material purchases and the maximum amount they might buy. The FY2020 potential purchases included: Antimony, Boron, Carbon Fiber, Cerium, Cadmium Zinc Tellurium (CZT), Electrolytic Manganese, Lanthanum, various explosives, Silicon Carbide Fibers, Tantalum, Tin, and Tungsten-Rhenium Alloy.
Aside from the buying, selling and storage of strategic and critical materials, NDS staff members also hold top secret security clearances for the work they do. Part of their job is to analyze open source intelligence, as well as, clandestinely collected intelligence, so, they can stay ahead of any developing issues that could constrain American access to materials contained in the NDS. For example, Indonesia is the largest seller of rubber to the United States. If there was a movement afoot to nationalize the rubber industry by the Indonesian government, this could disrupt the supply chain and impact DoD requirements for rubber. The NDS may determine the situation in Indonesia requires implementing a contingency plan to protect America’s supply chain of rubber.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com

RNSK Vol I, Edition 5
September 3, 2020
Transnational Organized Crime: What Makes It An American National Security Interest?
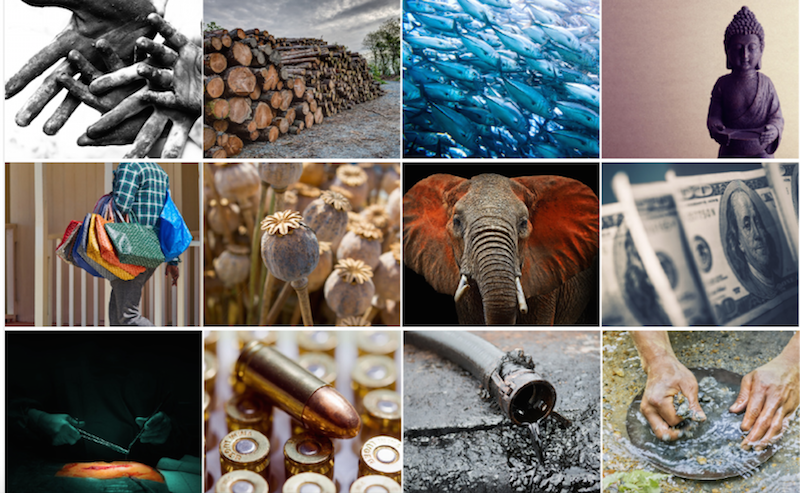 photo courtesy of Global Financial Integrity
photo courtesy of Global Financial Integrity
Introduction
The expanding size, scope, and influence of transnational organized crime and its impact on U.S. and international security and governance represents one of the most important challenges to nearly every country. During the past 20 years, technological innovation and globalization have proven to be an overwhelming force for good. However, transnational criminal organizations have taken advantage of our increasingly interconnected world to expand their illicit enterprises.
Threat Risks From Transnational Organized Crime
• Penetration of Foreign Government Institutions, Corruption, and Threats to Their Governance. Developing countries with weak rule of law can be particularly susceptible to Transnational Organized Crime (TOC) penetration. TOC penetration of states is deepening, leading to co-option in a few cases and further weakening of governance in many others. The apparent growing nexus in some states among TOC groups and elements of government—including intelligence services—and high-level business figures represents a significant threat to economic growth and democratic institutions.
• Threats to the Economy, U.S. Competitiveness, and Strategic Markets. Transnational Organized Crime threatens U.S. economic interests and can cause significant damage to the world financial system through its subversion, exploitation, and distortion of legitimate markets and economic activity. U.S. business leaders worry that U.S. firms are being put at a competitive disadvantage by Transnational Organized Crime and corruption, particularly in emerging markets where many perceive that rule of law is less reliable. The World Bank estimates over $1 trillion is spent each year to bribe public officials, causing an array of economic distortions and damage to legitimate economic activity. The price of doing business in countries affected by Transnational Organized Crime is also rising as companies budget for additional security costs, adversely impacting foreign direct investment in many parts of the world.
• Crime-Terror-Insurgency Nexus. Terrorists and insurgents increasingly are turning to Transnational Organized Crime to generate funding and acquire logistical support to carry out their violent acts. The Department of Justice maintains a classified report known as the Consolidated Priority Organization Targets (CPOT) list. The last time CPOT was declassified via a FOIA request was 2015. That edition of the CPOT listed a total of 63 organizations, 29 of which, are significant international drug trafficking organizations (DTOs) that threaten the United States, AND have links to terrorist groups. Involvement in the drug trade by the Taliban and the Revolutionary Armed Forces of Colombia (FARC) has been critical to the ability of these groups to fund terrorist activity. The U.S. Law Enforcement and Intelligence Community is concerned about Hezbollah’s drug and criminal activities, as well as indications of links between al-Qaeda in the Lands of the Islamic Maghreb and the drug trade. Further, the terrorist organization al-Shabaab has engaged in criminal activities such as kidnapping for ransom and extortion, and may derive limited fees from extortion or protection of pirates to generate funding for its operations. ISIS has also been very active in the TOC arena.
• Expansion of Drug Trafficking. Despite demonstrable counter-drug successes in the past 8-9 years, particularly against the cocaine trade, illicit drugs remain a serious threat to the health, safety, security, and financial well-being of Americans. The demand for illicit drugs, both in the United States and abroad, fuels the power, impunity, and violence of criminal organizations around the globe. Mexican DTOs have escalated their violence to consolidate their market share in the Western Hemisphere, protect their operations in Mexico, and expand their reach into the United States. In West Africa, Latin American cartels are exploiting local criminal organizations to move cocaine to Western Europe and the Middle East. Kenya, in Eastern Africa, has become a major distribution hub for heroin coming from Afghan DTOs to Europe and the United States. Many of the well-established organized criminal groups that had not been involved in drug trafficking—including those in Russia, China, Italy, and the Balkans—have now established ties to drug producers to develop their own distribution networks and markets.
• Human Smuggling/Trafficking. Human smuggling is the facilitation, transportation, attempted transportation, or illegal entry of a person or persons across an international border, in violation of one or more country’s laws, either clandestinely or through deception, whether with the use of fraudulent documents or through the evasion of legitimate border controls. It is a criminal commercial transaction between willing parties who go their separate ways once they have procured illegal entry into a country. The vast majority of people who are assisted in illegally entering the United States and other countries are smuggled, rather than trafficked. International human smuggling networks are linked to other transnational crimes including drug trafficking and the corruption of government officials. In the past few years trafficking in children has begun to pick-up.
• Weapons Trafficking. Criminal networks and illicit arms dealers also play important roles in the black markets from which terrorists and drug traffickers procure some of their weapons. As detailed in the 2010 UN Organization on Drugs & Crime report, The Globalization of Crime (Note: this report was a massive undertaking and cannot be replicated yearly, however a new one was in preparation for 2020 before the COVID-19 Pandemic, so it is unlikely to be published this year), the value of the documented global authorized trade in small arms (i.e.; handguns, rifles, shotguns, machine guns) has been estimated at approximately $2.08 billion in 2010, with unrecorded but legal transactions making up another $120 million or so. The most commonly cited estimate for the size of the illicit market is approximately 20% of the legal market. According to the head of UNODC, these “illicit arms fuel the violence that undermines security, development and justice” worldwide. U.S. Federal law enforcement agencies have intercepted large numbers of weapons or related items being smuggled to China, Russia, Mexico, the Philippines, Somalia, Myanmar, Mali, Somalia, Turkmenistan, Syria and Yemen. It is important to note this discussion does NOT include heavier weaponry, such as: Rocket Propelled Grenades, anti-tank rockets, heavy barrel machine guns (like the U.S. M2 .50 caliber machine gun, for example), fragmentation grenades, 40mm grenade launchers, mortars & field artillery.
• Intellectual Property Theft. TOC networks are engaged in the theft of critical U.S. intellectual property, including through intrusions into corporate and proprietary computer networks. Theft of intellectual property ranges from movies, music, and video games to imitations of popular and trusted brand names, to proprietary designs of high-tech devices and manufacturing processes. This intellectual property theft causes significant business losses, erodes U.S. competitiveness in the world marketplace, and in many cases threatens public health and safety. Between FY 2003 and FY 2010, the yearly domestic value of customs seizures at U.S. port and mail facilities related to intellectual property right (IPR) violations leaped from $94 million to $188 million. Products originating in China accounted for 66% of these IPR seizures in FY 2010. Estimates for 2020 are in excess of $450 million, and China still leads the pack.
• Cybercrime. TOC networks are now significantly involved in cybercrime, as it has become increasingly difficult to launder money, and/or defeat institutional security systems which are controlled by networked computer systems. Cybercrime costs consumers tens of billions of dollars annually, threatens sensitive corporate and government computer networks, and undermines worldwide confidence in the international financial system. Through cybercrime, transnational criminal organizations pose a significant threat to financial and trust systems—banking, stock markets, e-currency, and value and credit card services—on which the world economy depends. For example, some estimates indicate that online frauds perpetrated by Central European cybercrime networks have defrauded U.S. citizens or entities of more than $1 billion in a single year. According to the U.S. Secret Service, which investigates cybercrimes through its 31 Electronic Crimes Task Forces, financial crimes facilitated by anonymous online criminal elements, result in billions of dollars in losses to the Nation’s financial infrastructure. The National Cyber Investigative Joint Task Force, led by the Federal Bureau of Investigation (FBI), functions as a domestic focal point for 18 federal departments or agencies to coordinate, integrate, and share information related to cyber threat investigations, as well as make the Internet safer by pursuing terrorists, spies, and criminals who seek to exploit U.S. system.
• Information Warfare. The 2016 Presidential Election demonstrated that shadowy foreign government agencies, in concert with private TOC groups, have a significant capability of committing Information Warfare by exploiting America’s open society and means of mass communication. Common social media platforms, such as YouTube, Twitter, Instagram, TikTok, SnapChat, Facebook, Google, and others, have been infiltrated to influence public thinking. Other aspects of criminal information warfare include developing misleading documents, such as the now debunked dossier procured by the Democratic National Committee that attempted to implicate the Trump Campaign in colluding with Russia to rig the election. This dossier was actually used as evidence by the FBI to get a warrant to tap the phones of a Trump Campaign staffer. We are seeing just the tip of the iceberg in TOC involvement in information warfare. The allure of adversary governments using TOCs for these activities is simple: TOCs are adept at working in the shadows, below the radar, because getting caught is not as big of a problem as losing tens or even hundreds of millions of dollars in the process. TOCs could care less about their operatives going to jail; they are not happy about losing money. Adversary governments and terrorist groups are more than willing to pay for access to a TOCs well-developed network of money launderers, cyber criminals, black bag experts, etc. At this juncture, no one really knows how much money TOCs are pulling-in to facilitate information warfare projects. It now appears that some of these same shadowy TOCs are acting as conduits for money, planning and organizing insurrection and subversive activities in the U.S.
Ciao,
Steve Miller, IAPWE – Certified & Member
Managing Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com
RNSK Vol I, Edition 3
Written Statement of
William P. Barr
Attorney General
Committee on the Judiciary
U.S. House of Representatives
July 28, 2020

On July 28, 2020, United States Attorney General, William Barr, will testify in front of the Judiciary Committee of the U.S. House of Representatives. I want to call your attention to Attorney General Barr’s prepared statement released today, July 27th, and will be read into the Judiciary Committee’s proceedings by Barr. The unabridged content of AG Barr’s statement is shown below.
My purpose in bringing this statement to your attention is simply due to the near identical wording in his statement about the current spate of domestic violence issues, and the outcome of that violence, in comparison to my words cited in last weeks RNSK Volume I, Edition 2. It is important to me that my readers recognize that what I write is factual, and correctly analyzed. It is not a fanciful opinion of little value to the discerning public.
Here are some excerpts from Barr’s Statement:
“I want to address a different breakdown in the rule of law that we have witnessed over the past two months. In the wake of George Floyd’s death, violent rioters and anarchists have hijacked legitimate protests to wreak senseless havoc and destruction on innocent victims. The current situation in Portland is a telling example. Every night for the past two months, a mob of hundreds of rioters has laid siege to the federal courthouse and other nearby federal property.
What unfolds nightly around the courthouse cannot reasonably be called a protest; it is, by any objective measure, an assault on the Government of the United States.
Largely absent from these scenes of destruction are even superficial attempts by the rioters to connect their actions to George Floyd’s death or any legitimate call for reform.
Nor could such brazen acts of lawlessness plausibly be justified by a concern that police officers in Minnesota or elsewhere defied the law.
Remarkably, the response from many in the media and local elected offices to this organized assault has been to blame the federal government. To state what should be obvious, peaceful protesters do not throw explosives into federal courthouses, tear down plywood with crowbars, or launch fecal matter at federal officers. Such acts are in fact federal crimes under statutes enacted by this Congress.”
I invite you to read the rest of AG Barr’s prepared statement, and watch his Congressional testimony on July 28th at 10am EDT. Most major television news outlets will carry the proceedings live.
Ciao,
Steve Miller
Editor
The Report on National Security Kinetics™
Seattle, WA. USA
vietvetsteve@millermgmtsys.com


RNSK Vol I, Edition 1
Introduction
This is the premiere Edition of The Report on National Security Kinetics™ (RNSK). There are dozens of publications out there with content that touches on some of the RNSK Focus Areas, but, require regular monitoring of a half-dozen or more of them to cover it all. The RNSK format has been designed around a set of Focus Areas to help reduce a reader’s effort in keeping tabs on an important set of topics.
The RNSK Focus Areas have been selected by the editor based on 40+ years of experience as a U.S. military veteran, national security analyst, international business manager, writer, foreign policy researcher, college teacher, and military & presidential historian. It has been my honor to meet many women & men with similar backgrounds, including a shared belief in the importance of family, strong morals, human dignity, personal integrity, and putting country above self. Recognizing the Kinetic nature of National Security, factual & timely information related to the Focus Areas is an important factor to this editor and like-minded individuals.
The RNSK National Security Focus Areas are:
- Government-related Policy and Actions (U.S. & non-U.S.)
- Weapon Systems
- Intelligence Collection, Analysis and Counter-Terrorism
- Military Operations & Cyber Warfare
- Historical Commentary
These Focus Areas may not always be covered in each edition. Instead, the content will vary from one edition to the next based on what readers are asking for, global events, and the topical insights of RNSK correspondents with many decades of experience. RNSK content is:
- Reliable, well researched and factual;
- Written with minimal opinions, speculation, or someone’s Ouija board;
- Relative and timely, but, not a cyclical news source; RNSK has no competition-driven publishing deadlines.
The Need for Sources with Trustworthy, Verifiable Facts
With the widespread use of the internet, it puts a staggering level of content at our fingertips. The challenge for us, however, is determining the utility of what we read. Because our research & reading time is limited, it leads us to determine which information sources are most utilitarian, and fit the closest to our needs. For the serious consumer of useful web-based information, it is understood there is no “perfect” source, nor “one-size-fits-all.” We look for reliable information sources that provide the best content, without investing too much of our limited time and resources. In short, we want a good deal!
When I think about reliable information sources, it reminds me of my paternal grandfather, Albert Miller, a veteran of World War I and World War II. In between the wars, and for his last 20 years in the workforce, he was a pressroom manager for the Los Angeles Times. Although he was a loyal consumer of L.A. Times content, he also was a strong proponent of the philosophy, “believe only half of what you read, and nothing of what you hear.” He was a voracious reader of nearly everything he got his hands on. Coupled with pondering and introspection, he developed strong convictions based on objectivity. If he were alive today, he would have already applied his philosophy by carefully studying internet content for the favorable characteristics noted above. He would be scolding the public for not following his advice, and the global fallout over “fake news.”
History Repeats Itself
Prior to World War I, the average person was not overly challenged in differentiating between reliable and unreliable information purveyed to the public. Name brand public information back then included respected outlets such as the New York Times, Wall Street Journal, The Economist, and The Nation. After World War I, broadcast radio spread like wildfire across the globe, much the same way the Internet has in the past 20+ years. To illustrate the rapid spread of broadcast radio going into 1922, the year opened with only 28 radio stations in the United States. At the close of 1922, America could boast of having 570 commercial radio stations!
Radio broadcasting became so pervasive by the 1930s that Congress enacted legislation to form the Federal Communications Commission to regulate the industry. Just like television became the entertainment centerpiece in every home by the 1960s, radio held the same position from the 1920s through the 1940s. In the first half of the 20th Century, radio was literally the human lifeline to the rest of the world, the same as the Internet is today.
With the ever-increasing pace of a global society throughout the radio era, numerous people took the attitude that they were too busy, and did not have time to read a daily newspaper; the radio industry was more than happy to fill the gap. Radio carried the news, weather, sports, church services, music, and programmed entertainment, to name a few. Back then, different types of broadcasts were discernible…news programs and fictional entertainment were done in different styles. The overreliance on radio for all aspects of life spawned a common phrase that carried the force-of-truth behind it, “hey, I just heard on the radio…” If you heard it on the radio, it has to be true, right?
The bubble of truth in radio was burst in 1938 with the broadcast that came to be known as, “The War of the Worlds.” A 22-year old actor, Orson Welles, conducted a radio broadcast meant to be science fiction entertainment, but, it was delivered like a real newscast. Millions of people heard Welles’ “report,” and actually thought the Earth was under alien invasion! Even though Welles’ intent was entertainment, the public’s reliance on radio allowed them to be duped into thinking they were under alien attack. If you heard it on the radio, it has to be true, right?
Fast forward this to the internet age, but, with public overreliance on web-based content instead of radio, it has once again allowed agents-of-manipulation to blur the lines between fact and fiction. An unchecked social media was/is the perfect place to sow disinformation and blur-the-lines. In simple terms, with the veneer stripped back, it is slick, subtle lying; which isn’t very “social” by most people’s standards. This is evident in all the stories about “fake news” and the Information Warfare conducted during the 2016 Presidential Election. But, make no mistake, the blurring of fact and fiction seen in the past two years has nothing to do with entertainment, nor is it strictly one-upmanship between competing web-based information sources.
Duping the public with disinformation during the age of radio, or today’s internet, is not just information warfare; the root of the matter goes much deeper. So, it is true; history does repeat itself, but, why?
Web-based information distortion in some cases is an act-of-war; much like the information subterfuge undertaken by both sides in World War II. Let’s call it what it really is, a term that does not mince words…Espionage. It may not be a shooting war, but, it is warfare, nonetheless. The circumstances behind public communication in wartime England may have had its Fascist & Communists intriguers who angered government authorities and were carefully watched. The moment they crossed-the-line from just stirring things up, to proof of subversion, they were going to jail for espionage, at the least.
How Does This Relate to the RNSK?
The foregoing discussion bothers me…it bothers me a LOT. We can all agree that fiction is entertaining, but, not when we are looking for, and expecting to find the facts. But, even when we successfully cull-out fictional information, facts may still not be the facts. What someone says or writes may not be pure fiction, or manipulated fake news, but, what about intentional or unintentional co-mingling of fact and opinion? Any purveyor of information, regardless of media type, if they want to be seen as a viable source of factual information, they must exercise overt care in identifying when something is an expressed opinion, versus a confirmed fact. Whether a purveyor of opinion is honestly expressing just their opinion, it can and does, influence other people’s thinking and opinions. Expressing an opinion that is co-mingled with fact, is a disservice to the consumer, at best; at worst, it intends to convince someone how to think and act.
When it comes to writing and publishing the RNSK, the intent is to avoid the foregoing communication/information problems by the guidelines previously mentioned, to wit:
- Reliable, well researched and factual;
- Written with minimal opinions, speculation, or someone’s Ouija board;
- Relative and timely, but, not a cyclical news source; RNSK has no competition-driven publishing deadlines.
So, if you have an interest in rounding-out your national security knowledge in today’s kinetic environment, and want the confidence of knowing the content is based on the foregoing parameters in a defined set of Focus Areas, and has been written with an eye toward the values imbued by America’s Founding Fathers, then The Report on National Security Kinetics™ is what you need…Welcome!
This is enough for now; the introduction has been done. Rather than trying to include an actual content article buried at the bottom of this premiere edition, where it likely would get lost, we will begin publishing informational content in the next edition. In the beginning, RNSK will be published bi-weekly. If a published article is prepared by a correspondent other than the editor, their name/credentials will appear at the end of it. Unless otherwise noted, all other content is by the editor & chief correspondent.
Ciao,
Steve Miller
Editor
The Report on National Security Kinetics™
Seattle, WA. USA
http://www.millermgmtsys.com

Why was the Lockheed Martin F-22 Raptor developed?
After the Vietnam War the Pentagon paused for a moment to consider the lessons learned. More than any other service branch during the War, the U.S. Air Force was in a constant state of change for 12 years – from 1963 to 1975. Fortunately, there were several Air Force leaders with the foresight to recognize somebody better be taking notes throughout the conflict!
The “note taking” was formalized into a standard reporting format. Within the Pacific Air Force (PACAF) headquarters in Hawaii, one of the major departments was the Deputy Chief of Staff, Plans and Operations, headed by a Brigadier General. Under DCS, Plans/Ops, there was a group known as the Tactical Evaluation Directorate led by a full colonel. The TED had numerous ongoing duties, and several specialized projects. One of the specialized projects had the rather innocuous-sounding title of: “Operations Analysis Division.” The OAD actually had just one real responsibility, and that was: Managing a Top Secret project known as Operation CORONA HARVEST; it was responsible for researching, preparing and writing what became known as “CHECO Reports.” CHECO stood for: Contemporary Historical Evaluation of Combat Operations.”
CHECO Reports totaled more than 250 by time South Vietnam capitulated in April 1975. The reports were solely focused on the various combat activities the U.S. Air Force conducted in Southeast Asia. Some CHECO topics were one-off, such as Operation LUCKY TIGER in Laos. Other topics ended-up with multiple reports written as a series of periodic updates from 18 months to two years apart, with all of them revolving around the central theme. For example, the ROLLING THUNDER bombing campaign in North Vietnam ran from March 1965 to the autumn of 1968. During the three and a half years of operation, ROLLING THUNDER had four CHECO reports – the original one, and three update reports.
About 65% of the CHECO reports were classified Secret. The remaining reports were mostly Top Secret. Several of the Top Secret reports were so sensitive that the missives also carried a classified code word, and was designated SCI (sensitive, compartmented information). The U.S. had several free world nations participating in Vietnam combat operations, too, such as South Korea & Australia. Generally speaking, most classified information was freely shared amongst the partners; but, the Pentagon felt some topics were best left unsaid. To that end, an administrative marking of “NOFORN” was also stamped on the document. NOFORN stood for “NO FOReign Nationals.” Unless you were an American citizen, you were not permitted to see the report; this was regardless of someone’s security clearance.
Understanding the background and context of the CHECO reports helps understand the next aspect. It wasn’t until the late 1990s that some of the CHECO reports had been requested by the public through USAF’s FOIA program managed from the Pentagon. The significance of the late 1990s is FOIA requests for one of the reports was finally being allowed to go through the MDR (mandatory declassification review) process. Previously, CHECO report FOIA requests came back to the person asking for it, stating the contents were still too sensitive to declassify. The vast majority of the reports had certain exemption requirements from being declassified through the routine, automatic downgrading process. By the late 1990s the majority of the CHECO reports had moved out from under the declassification exemption laws and could be submitted on a FOIA to commence the MDR effort. On average, a requested MDR on a CHECO report had a throughput time of two years or more. Although the declassified reports had portions redacted, they were still easy enough to learn from without a lot of information “ending-up-on-the-cutting-room-floor.” Researchers, like me, immediately saw the treasure trove of useful information available from the CHECO reports.
Although Vietnam War historians like myself really appreciated having access to all the CHECO reports, the real beneficiaries were the military aviation community throughout the War and for decades afterward. But, how does this relate to the F-22? Simply put, important lessons on the future of air combat were memorialized in the CHECO reports. The following dialogue paraphrases some of the more salient points as it pertains to the ultimate combat design configuration of the F-22. Keep in mind, the F-22 is labeled as a “5th generation fighter jet.” There are many lessons learned in air warfare from Vietnam that were incorporated into 4th generation fighters, such as: the F-15, F-16 and F-18.
1. The Air Force entered the Vietnam War with the Republic F-105 Thunderchief as its premier tactical fighter-bomber. The fighter aspect of an F-105 was actually not much more than its DOD alphanumeric model identifier, and it was about the same size as other fighter-style aircraft designed in the late 1950s and early 1960s. From there, the similarities ended. The F-105 was not built for air-to-air combat. It was also not built to be caught by another fighter, AAA cannon fire or SAMs. The reason why is: the plane was extremely fast and was meant to perform low-level penetration, nuclear weapons delivery. In Vietnam, however, USAF lost more than 400 F-105s; that’s one-third of the total number built. By 1970, USAF had sent all of the tactical bomber variants home. Total losses would have easily eclipsed more than half the total F-105 fleet if they had continued to fly in SEA combat. The plane’s role in Operation ROLLING THUNDER was regular, tactical bombing with conventional munitions, and it flew sub-sonic into the target area at the typical tactical bombing altitude of 5,000 to 8,000 ft AGL. That altitude was the “sweet spot” for 57mm cannons slaved to an automatic-tracking gun laying radar. Many people have heard how deadly SAMs were in Vietnam; but, the Navy and Air Force both suffered the highest loss percentages from 57mm AAA. Although the F-105 was a rugged plane, it lacked adequate ECM warning gear, and the aircraft design was not done in a way that anticipated the pilot & plane having to fight their way into and back out of the target. One of the plane’s greatest design vulnerabilities was not separating its system redundancies far enough apart to prevent knocking the plane down with one cannon round that could eliminate the primary and back-up flight control equipment. These lessons learned were incorporated in the A-10 and all other fighters and attack aircraft that followed Vietnam. These concepts went into the F-22, too.
2. Another important outcome of the War was recognizing the electronic battle space was an iterative process for both sides. The threat density environment of North Vietnam became the most heavily defended airspace in history. During the Cold War, Electronic Warfare equipment installed aboard tactical aircraft was bulky, highly complex & required constant maintenance by factory engineers on permanent duty at U.S. Air Bases in Thailand; the ECM pods were very expensive, and could not be produced fast enough to protect every aircraft on its own. For the better part of 20 years, especially during Vietnam, General Electric and Sanders & Associates were the premier defense contractors in the field of airborne EW; especially radar jamming transmitters.
For the most part, military aircraft developed and manufactured in the 1950s, 1960s & early 1970s, were tailored to perform a certain role in air combat. The B-52 Stratofortress was one of the few planes designed to be self-contained; including the ability to electronically fight its way to the target and then back home again (although fighting its way out from the target was highly suspect by some experts). The B-52 is a huge plane with enough onboard room to squeeze in newer and better functioning equipment. Fighter jets, however, were so space-limited that it was virtually impossible to add extra systems without compromising the plane’s ability to fight in other aspects of air combat. Tactical fighter-bombers used in Vietnam – like the Republic F-105 – had to have outside support from special mission aircraft to help the “Thuds” live to fight another day.
The 7th Air Force commander at Ton San Nhut Air Base, Saigon, was General William Momyer. Momyer and his operations staff ultimately developed a mutually supporting strike package for ROLLING THUNDER bombing operations. The 7th Air Force tabbed this new bombing methodology as an “Alpha Strike.” The Alpha Strike had three primary objectives:
A. Completely destroy the target(s);
B. Don’t lose any aircrews or planes;
C. Ensure that another Alpha Strike did not have to go back to the same target again.
The Alpha Strike bombing package was developed and first saw use in January 1967 for targets within a 50 mile radius of Hanoi. The F-105 Thunderchief was the principal strike bomber used in the first half of the war. Regular usage of the Alpha Strike continued until the 1968 bombing halt ordered by President Johnson. It went back into use in February 1972 to force North Vietnam back to the bargaining table to complete a peace agreement. The vulnerability of the F-105 was the main reason for the Alpha Strike package. The F-4 Phantom replaced the F-105 as the principal strike bomber by 1972. The remaining F-105s were converted to the two-seat “Wild Weasel” (Iron Hand) AAA defense suppression configuration.
In order to knock-out two major targets, such as a railroad yard and a railroad bridge, 16 F-105s (or F-4s) were assigned to each target, 32 total, to bomb the targets five minutes apart. To prevent the previously seen F-105 losses, it took an additional 54 aircraft of various types, as much as five hours before and after the strike, to deter the excessive fighter-bomber losses! No doubt, an Alpha Strike put many more airmen at risk than just the strike aircraft.
The Alpha Strike Package launched its first aircraft five hours ahead of the attack aircraft. North Vietnam had notoriously bad weather – cloud cover about 85% of the time. The weather was also prone to change quite rapidly. So, two flights of two RF-4Cs were fragged for a weather reconnaissance sortie in the general area of the two targets for that day. If the weather was bad, and the base weather shop had no indications of it clearing before TOT, the Alpha Strike was scrubbed.
Two hours prior to TOT, a flight of four F-4Ds, fragged for “SARCAP,” (Search and Rescue, Combat Air Patrol) were launched with an “on-station time” of one hour pre-TOT, and remained on-station until 30 minutes after completing the 2nd target’s strike. The primary purpose of SARCAP was surveillance of the target and ingress/egress routes for possible American aircraft going down. Often times the fragged attack aircraft were so busy doing their jobs, they may not have seen a plane go down. SARCAPs had no other purpose than to track aircraft target ingress and egress, looking for planes in trouble, or were going down, or had already crashed. SARCAPs notified the ABCCC of a downed plane for purposes of launching a CSAR attempt.
One hour prior to TOT, two F-4Ds were launched for BARCAP. Barrier Combat Air Patrol had two purposes: 1.) Make sure American aircraft did not wander into restricted airspace; 2.) There were numerous support aircraft lingering over Northern Laos, such as, tankers, CSAR choppers, etc. They were at-risk if the North Vietnamese sent MiG-21s to go make trouble for them. BARCAP kept bogies away from the holding area.
Ten minutes prior to TOT #1, eight F-4Ds passed between the target areas and the heaviest concentration of enemy AAA and SAM tracking radar, dumping a heavy cloud of electronic countermeasures chaff to defeat enemy tracking radars.
About 45 minutes prior to TOT, two F-105s or F-4Ds, were launched for IRON HAND missions. IRON HAND was responsible for attacking enemy radar sites. This type of mission was also known as, “SEAD” (Suppression of Enemy Air Defense). Flying this dangerous mission earned the aircrews and planes the unofficial title of “Wild Weasel.” Four more aircraft at staggered intervals would replace the first two Wild Weasels.
At the same time the Wild Weasels entered the operational area, four F-4Ds also arrived to fly MIGCAP (MiG, Combat Air Patrol). Since the F-4s were such a versatile aircraft, they could be configured solely for air-to-air combat. The planes primarily used Sidewinder heat-seeking missiles, and Sparrow radar-directed missiles. All of the F-4s up to, and including the “D” model, were not equipped with a conventional automatic weapon system. Aerial combat in North Vietnam proved the F-4s still needed a close-in, rapid fire cannon. A temporary pod was slung underneath the plane to carry a 20mm Gatling gun. The F-4Es came standard with a M61 Vulcan 20mm Gatling gun built inside the fuselage.
The North Vietnamese had limited resources in the area of fighter jets capable of defeating the F-4. The MiG-19s were used throughout the War, and did not match-up consistently with the F-4s. The Mig-21s did not come along until the 3rd year of the War; they were better than the MiG-19, but still mismatched in many ways against the F-4. Qualified fighter pilots were just as scarce as the jets they flew. Eventually, due to losses, enemy fighters only came up to fight sporadically. North Vietnamese fighters did not actually have to shoot down one of the bomb-laden American planes. They could easily break-up the strike element by flying through their formation, and watch everyone scatter. Similarly with MIGCAP planes, they did not need to shoot down any MiGs; just disrupt their efforts to cause trouble.
Each of the two, 16-plane strike packages also had four F-4s as escort planes to protect the attack aircraft through the target area, and back out again.
The strike packages also had four EB-66Es carrying 21 jamming transmitters per plane to “gum-up” the North Vietnamese air defense radars. After the missions were over, two RF-4Cs flew over the targets for BDA photos.
The foregoing discussion clearly shows the Alpha Strike package was not the air combat mode-of-choice; it evolved as a necessity for getting the job done. Recapping the primary reasons for developing the concept were:
A. Completely destroy the target(s);
B. Don’t lose any aircrews or planes;
C. Ensure that another Alpha Strike did not have to go back to the same target again.
The Alpha Strike consisted of 86 aircraft…32 planes to do the actual bombing and 54 more to accomplish items A, B & C above. There were many other support elements in the air during an Alpha Strike, but not considered part of the strike package, such as: KC-135 tankers, EC-130 ABCCCs, HC-130 CSAR directors, HH-3E CSAR helicopters, and A-1 “Sandy” CSAR escorts. This put a huge number of airmen’s lives at risk. The aforementioned CHECO reports bore-out all of these issues. Coming out of Vietnam, air combat experts realized the U.S. military could not fight another air war in this manner. The Fulda Gap and an air-supported ground war against the Warsaw Pact nations was the overriding thought on everyone’s mind.
Aside from the lessons learned in Item #1 above about designing aircraft to be more rugged and able to withstand battle damage, Item #2 demonstrated that if you wanted to reduce the number of support actors on an airstrike, the strike aircraft themselves had to be more self-sufficient by at least being the most superior, high performance aircraft over the battlefield. Improving aircraft survivability and performance coming out of Vietnam were known issues. The problem was: engineering technology to solve all of the problems did not exist, yet. Some of the challenges would take more than 10 years to develop realistic solutions.
The engineering challenge nearest to solving was aircraft performance. The Grumman F-14 Tomcat, McDonnell-Douglas F-15 Eagle and General Dynamics F-16 Viper were the immediate focus of aerodynamics and performance improvement. For this discussion I will focus on the F-16 because it included the most innovative, cutting edge aeronautical engineering features beyond other 4th generation jet fighters.
The USAF F-16 procurement specification issued to General Dynamics required a supersonic airplane that did not experience airspeed decay during radical combat maneuvering. The most common airspeed decay inherent to all planes was a maximum performance climb to higher altitude. At maximum power in a steep climb, airspeed could not be maintained. To overcome airspeed decay in a steep climb, it boils down to an aeronautical engineering metric known as “thrust-to-weight” ratio. Until the F-15 and F-16 came along, high performance jets and their installed jet engines generated a maximum thrust level that was below the weight of the aircraft. The two-engine F-15 and single engine F-16 both have greater than 1:1 thrust-to-weight ratios. The net result is an aircraft with the ability to accelerate its airspeed, even in a steep climb. If a F-16 pilot wants to shake-off an adversary, all he has to do is make a max power, steep climb and simply “walk away” from the bogie.
The next major design feature was aircraft maneuverability. In order for the F-16 to outmaneuver an enemy aircraft, regardless of who was chasing who, designers determined if the Air Force truly wanted an aircraft that could not be outmaneuvered, then sustained 9G turns were necessary. Until the F-16 came along, no aircraft or pilot could sustain the force of 9Gs. One of the most critical design features of all previous aircraft was making the plane aerodynamically stable. Without getting too technical, conventional thinking prior to the F-16 was: planes needed to be aerodynamically stable to make them easier and safer to fly. Planes were designed with the inherent ability to maintain straight and level flight; even without control inputs from the pilot.
The end result from an aerodynamically stable aircraft was simply that, achieving sustained high G performance was going to yield one of three basic outcomes, if not all three:
1. The pilot will black-out;
2. The plane will depart controlled flight;
3. The plane will experience a structural failure that leads to destruction.
I won’t spend a lot of time discussing the human factors engineering that went into the F-16 cockpit design. The two most obvious features for the pilot is an ejection seat built on a 30 degree recline – somewhat like your Lazy-Boy chair in the living room. This slowed the physiological phenomena of the pilot’s blood leaving the brain too rapidly and causing a black-out from sitting upright. The second factor took into consideration that in a 9G maneuver, a 170 lb pilot is pressed into his seat with a force exceeding 1,500 lbs, making any sort of body movement very limited. To that end, the F-16 uses a sidestick controller instead of the traditional stick in the floor between the pilot’s legs.
In order to avoid structural failure in a 9G turn, the airframe had to be strengthened using new technology metals design and fabrication. The last maneuverability issue is an aerodynamically stable aircraft departing controlled flight at high G loading. If the pilot is protected from blacking-out, and the airframe can withstand the high G forces, then how can you recover an aerodynamically stable aircraft when it departs controlled flight? A pilot’s odds of success are pretty low using conventional, pilot-actuated mechanical flight controls. The resulting F-16 design concept was to make the plane aerodynamically unstable to achieve the maneuverability needed, and manage the attendant high G forces. Design engineers recognized the only way to maintain control over an aerodynamically unstable aircraft was to use a computer system to make and send hundreds of micro-adjustments per second to the flight control surfaces, and completely eliminate the mechanical linkage flight controls. The F-16 became the first aircraft with a 100% fly-by-wire flight control system. Although there were other less significant lessons learned from the Vietnam CHECO reports, these are the major achievements implemented in the 1970s-designed, 4th generation aircraft.
3. Beyond what has been discussed in Items #1 & 2 above, the third major lesson learned was coping with the enemy’s ever changing “Electronic-Order-of-Battle” (EOB). A more colloquial term for this is “Electronic Warfare” (EW). Actions taken to defeat an enemy’s EOB (EW) system (program, suite, process, et al) are known as “Electronic Counter-Measures” (ECM). Further enemy action to reduce or disable the other side’s ECM, is called “Electronic Counter, Counter-Measures” (ECCM). The topic of EW, as it pertains to the Vietnam War, was written about extensively in the CHECO reports. Since the end of the War, there are at least five independently authored books I can think of related to EW in Southeast Asia. In some cases the available reading materials were written for technical experts; but, there are several written for consumption by the average layman. This narrative is not the place to educate the reader about radar engineering. Having been a radar systems engineer for four decades, and an author of other writings about EW, I can strike the right content balance to move the story along.
When I was a kid growing up in the turbulent Cold War years of the 1960s, there were several items we had to have as a rite-of-passage. For example, even though only a small percentage of American teenagers and young adults actually went to the Woodstock Music Festival in 1969, it was no excuse for everyone else to not buy the two record albums released of all the songs. Similarly, a teen was not a teen if you were not a regular reader of MAD Magazine. One of the most prominent cartoon strips featured in every issue was the Cold War parody of “Spy-vs-Spy.” The basic theme of the strip was a white-clad spy, and a black-clad spy who were at constant odds with each other to get-over on the other guy. Each month the two spies alternated back n’ forth with one beating the other using his cloak n’ dagger tradecraft. If the two characters were mere mortals, they would each have “died” several hundred times over the decades. The cartoon was one of my favorites. But, taking the Spy-vs-Spy gag and superimposing it over the EW battle raging in Vietnam between the Communist North, and the Free World countries like the U.S. and Australia, it suddenly was not very funny anymore. It was Spy-vs-Spy with a deadly outcome.
When the U.S. began its large scale ROLLING THUNDER bombing campaign in North Vietnam, it was the first time American aircrews experienced aerial combat where the EOB became an overwhelming factor impacting air combat operations. Some of the most prominent electronic warfare deficiencies the Pentagon had to grapple with, included:
1. Not having an AWACS-sort of capability to provide radar surveillance of North Vietnamese airspace;
2. The Communist’s frontline SAM made by the Soviets, the SA-2 Guideline missile, contained a special proximity fuse warhead to detonate the SAM when it came close to the target. The U.S. had no knowledge of the operating & technical characteristics of the proximity fuse;
3. The American’s passive ECM Radar Homing And Warning (RHAW) gear was not installed on all in-theater aircraft when the War started. Further, the RHAW did not have the capability to detect all of the various radars used in the enemy’s air defense network;
4. None of the Navy’s or Air Force tactical bombers (i.e.; F-105, A-4, A-6, F-4) were equipped with their own radar jamming equipment;
5. Likewise, the tactical bombers did not carry self-contained ECM dispensers for chaff, or later on, for flares;
6. Each type of aircraft going up North had its own weaknesses in terms of radar detectability, airspeed and/or agility to avoid getting shot down.
All of these deficiencies had to be addressed and either eliminated or mitigated as much as possible. Many of these problems led to the Alpha Strike concept as one of the immediate band-aids to apply until more permanent solutions could be sought and introduced to the field. By time the War started winding down, it was obvious by reading the CHECO reports that air combatant commanders began pushing hard for any plane designed to fly in denied or semi-permissive airspace to have standalone capability…no more Alpha Strikes. Ultimately, this was the end design goal for the F-22 Raptor – a plane that could fight and take care of itself.
As previously discussed about the F-16 and other 4th generation fighter/bombers, the Pentagon sought whatever immediate or near-term technology enhancements possible. There were two major areas requiring a quantum leap that would require nearly a decade or more to achieve closure on both of them in terms of a tactical strike fighter (i.e.; the F-22). They were:
1. Design an aircraft that is virtually undetectable by enemy radar;
2. Design and install a fully integrated passive and active EW/ECM aircraft self-defense system.
Item #2 was a tall order coming out of Vietnam in the mid-1970s for many reasons. I’ll cover that discussion after disposing of item #1.
The central nervous system of any anti-aircraft defense system is the array of various radars that are each designed to perform a certain aspect of the AAA Electronic Order of Battle. During the Vietnam War there were five primary radars designed and built by the Soviets and sold to the North Vietnamese. Throughout the 11+ years of active, American air combat operations in Southeast Asia, Soviet Army technical detachments led by a warrant officer were assigned to every one of the North Vietnamese AAA battalions. The Soviets used active duty military personnel as in-country technical representatives instead of the American preference for defense contractor field engineers.
All Soviet-made combat equipment (including planes) was given a phonetic identification name developed by the NATO countries. For example, a AAA fire control radar carried a code that always started with an “F.” Search radars had names using the letter “S.” All of the anti-aircraft radar systems were mounted on trailers for quick transport from one AAA site to another. The primary long range search radar was called “Spoon Rest.” Spoon Rest operated in the VHF frequency range and could reach out more than 200 miles to detect aircraft. Spoon Rest’s primary job was merely aircraft detection in terms of azimuth and the target’s distance. Spoon Rest’s detection data was passed verbally by radio or ground line data links to the AAA battalion’s HQ operations center. The operations controllers determined which AAA site to hand-off the new bogie to.
Located at the AAA sites with weaponry were several other radars. The next radar to begin monitoring enemy aircraft had the NATO name, Flat Face. Even though Flat Face carried a code name for a fire control radar, it was not directly controlling a weapons system. It carried a NATO fire control code name because Flat Face radars were generally co-located at the fire control radar sites, which were in direct control of live weaponry. Flat Face operated in the upper UHF frequency range and was capable of the same results coming from the Spoon Rest search radar. Flat Face radars were used as acquisition radars. They had the added feature of also determining a target’s altitude. One of the most important features of Flat Face was its ability to feed electronic target data through local, shielded ground cables directly over to the target tracking, fire control radars. The advantage here was: the fire control radars could leave their transmitters turned-off and remain undetected. Flat Face’s radar target feed automatically slaved the fire control radar antennas to point directly at the incoming target. When the target was within the lethal envelope of the AAA weapons, such as: SAMs, 57mm cannons and others, the fire control director could flip the transmitter switch on and the antennas were already pointing right at the target. Within four-to-six seconds a target could be locked-on and the weapons released.
For most of the War, North Vietnam used two types of SAM fire control tracking radars: The Fan Song B and Fan Song C. Both were automatic tracking radars that kept the target locked-on while the SAM missile was zooming toward the target. The Fan Songs sent out a radar stream of one-way guidance commands to steer the SAM into the target. Towards the end of America’s stint in direct combat operations in late 1972, the Soviets sold their latest SAM guidance & tracking radar, NATO code named – “Low Blow.” This system also came with a new missile called the “Goa.” The Goa and Low Blow were custom-designed to shoot down low flying aircraft.
The fifth AAA defense radar was known as “Firecan.” Once again, it was an automatic tracking radar, but not for SAMs; it was used as a gun laying, fire control radar. The Firecan was most commonly used to control a battery of multiple, single barrel 57mm cannons, or a Zsu-23, a deadly, truck-mounted, quadruple barreled array of 23mm cannons.
The five AAA defense radars just listed – the Spoon Rest, Flat Face, Fan Song B, Fan Song C, and Firecan were the primary threats throughout the war; the Low Blow came later. With this combination of formidable EW hardware, EW experts at the DIA (Defense Intelligence Agency) lamented that things would be much easier if the Soviet-made EW radars never “saw” American combat aircraft in the first place. I will circle back to passive and active ECM in a moment. But, first, the Pentagon decided to take-on the challenge of making a plane invisible as it flew through denied, enemy airspace. The seeds of stealth technology were firmly planted and embarked upon by the mid-1970s: Let’s design and build an “invisible” airplane. The result would be the Lockheed F-117 Nighthawk.
Radar’s infancy occurred during WW II with great strides made by both British and American engineers. At the time, both allies were only flying propeller driven aircraft in combat. The physical configuration of a plane’s airframe, wings, and other appendages was mostly about combat functionality, first, and then achieving a certain semblance of aerodynamics and flying stability. From the standpoint of whether, or how easily, a plane was detected by a radar system, was not of prime consideration in the 1940s.
After the war, Great Britain, the United States, and the Soviet Union all pursued jet aircraft RDT&E at a vigorous pace. With jet planes breaking the sound barrier at speeds up to 200% faster than the speediest WW II fighter-bombers, such as: the Vought F4U Corsair, Lockheed P-38 Lightning, North American P-51 Mustang and the deHavilland DH.98 Mosquito, a low-drag, aerodynamically stable airframe was critical. In parallel with jet engine & aircraft development, radar engineers were predominantly focused on improving equipment reliability, adapting radar technology to new applications, and researching the characteristics of different operating frequencies, power levels, pulse widths, etc. For the most part, up to and through the Korean War, common thought leaned toward an airborne target’s radar detectability being based on the aircraft’s physical size. Engineers, however, were discovering that increasing or decreasing a plane’s size did not necessarily mean a proportional change in the magnitude of its radar return echo. More study was needed. During this timeframe engineers began to refer to an aircraft’s radar detectability using the unit-of-measure known as, “Radar Cross Section” (RCS).
Extensive RDT&E was conducted on aerial target RCS during the 1950s; it still continues today. Speaking in generalities, if a radar transmitter/receiver is in a fixed position with its antenna pointed at a fixed target (like a parked aircraft), such that the side of the plane and direction of the radar antenna are perpendicular to each other, the transmitter’s radar pulse will bounce (reflect) off the side of the plane with most of the reflected energy echoing back to the radar receiver on a 180 degree return path. A layman’s example would be throwing a tennis ball against a wall with the ball’s flight path perpendicular to the wall. The resulting bounce back tends to come back to the spot where the thrower is standing. The radar’s transmitted power decreases drastically by time it detects the plane and is reflected back. The echo signal, however, is not even going to reflect all of the energy back to the radar receiver that arrived at the plane (target). Some of the remaining return echo’s signal will scatter in other directions and rapidly dissipate.
Continuing the tennis ball example, if you throw the ball against the wall at an oblique angle to the wall, the return bounce will come off of the wall in another oblique angle, not come back to you. Radars and targets have a similar behavior, such that if the transmitter pulse hits the plane at an oblique angle, then the majority of the return signal will obliquely reflect-off of the plane’s side and the radar receiver will be lucky to get even a fraction of the reflection back to it. Of course, if the radar antenna is moving around, and its airborne target is moving, too, then the reflected signal is going to be a constantly changing value. This was an important concept behind calculating a plane’s RCS value.
As radar and aerial target R&D continued in the 1950s and early 1960s, other phenomenon about RCS was manifested. These factors included:
1. A more rounded fuselage tended to reduce the RCS value;
2. Non-blended aircraft appendages, such as under-wing ordnance, bomb bay doors and propellers increased RCS;
3. Jet engine intakes and even the first stage compressor blades reflected more energy than expected -, driving up the RCS value;
4. Engineers also discovered that the type of paint on the plane could increase or decrease the RCS;
By 1962 it was generally apparent among Pentagon air power proponents, particularly the Air Force, that all military aircraft needed to undergo RCS testing during their full scale design & development phase. To that end, the Air Force Systems Command directed one of its R&D labs, the Rome Air Development Center (RADC) at Griffiss AFB, NY to begin developing a procurement specification for issuing a USAF contract to a DOD prime contractor for the design, development, manufacture, and installation of specialized radar equipment to stand-up a dedicated RCS test facility.
In December 1962 RADC issued a contract to General Dynamics, Ft. Worth Division, as the prime contractor for the RCS facility. The project and the completed facility became known as the “Radar Target Scatter Facility.” Ultimately the facility went by its nickname, “RAT SCAT.” It was (and still is) critical to locate the new RAT SCAT site where there was virtually no other random radar signals or problems with RFI (Radio Frequency Interference) that could skew the sensitive RCS test results.
The site chosen for RAT SCAT was located in the middle of the Army’s White Sands Missile Range near Alamogordo, New Mexico. To be specific, the new site would be built in a spot known as Alkali Flats, approximately 20 miles west of USAF’s Holloman AFB. RAT SCAT’s outer perimeter fence was two miles square, or 1,280 acres. Inside the main perimeter was the actual 416 acre site with all of its equipment, buildings and the three-position target range. In order to keep the RFI to a minimum, the Air Force chose Alkali Flats for its location in a depression amid White Sands 70′ tall sand dunes it was famous for. Construction crews had to cut the new, 20-mile long road to the site through the sand dunes. Building the new road to the site was almost as difficult as it was to design and build RAT SCAT’s sensitive radar equipment. Construction crews had to remove a half million cubic yards of sand to cut the road through the dunes. By December 1964, RAT SCAT was declared operational, and General Dynamics engineers were contracted to run the site & do the RCS testing. RAT SCAT is still the Government’s main RCS test facility after 51 years of operation.
After RAT SCAT opened for business, much of their initial work involved RDT&E for the more generalized characteristics of Radar Cross Section analysis. Eventually, all military aircraft in future years would have a date with the RAT SCAT team for RCS testing. In 1965, however, neither the U.S. Navy, nor the Air Force had any fighter-bombers undergoing their preliminary design and development. Aircraft in active use in Southeast Asia (or soon would be), such as the A-6 Intruder, A-4 Skyhawk, A-5 Vigilante, F-4 Phantom, F-111 Aardvark, F-8 Crusader, A-3 Skywarrior, and the EB-66 Destroyer, had already completed their production run, were still in production, or were well past their CDR (Critical Design Review) and their engineering configuration was locked-down. The only fighter-bomber used in Vietnam that first flew after RAT SCAT opened was the LTV A-7 Corsair II. The A-7 though, was not a completely-from-scratch aircraft whose design may have benefited from RCS testing. The A-7’s profile was deliberately designed using the Vought F-8 Crusader’s silhouette. There would not be a lot of value testing the RCS of the A-7; the F-8 dictated what the A-7 would become.
The first new weapons platform to have the full benefit of RAT SCAT testing was the Grumman F-14 Tomcat; its maiden flight was in 1970. Then the Fairchild A-10 Thunderbolt II, the McDonnell-Douglas F-15 Eagle, and finally, the General Dynamics F-16 Fighting Falcon; they all derived benefit from RCS studies conducted at RAT SCAT.
As referenced earlier, two of the most complex issues about EW coming out of Vietnam was making an aircraft more difficult to detect on radar, and ECM equipment to defeat the enemy EOB. Considerable data had been compiled, including RAT SCAT testing, on the cause of an aircraft’s large RCS, and what could be done about it. When ECM, EW, RCS, etc., began to appear in periodicals such as Aviation Week & Space Technology, the media quickly dubbed this genre as “stealth technology.” For the military & engineering EW community, stealth’s more formal label was “Low Observables Technology,” or simply “LO,” for short. Although much of the discussion thus far has focused on airborne target detection via radar, LO technology also covered other aspects of EW based on non-radar means. Two examples include an aircraft’s infrared (IR) heat signature and RF emissions emanating from a target aircraft, such as the plane’s radios, radar, or navigation system.
In 1976 Lockheed was issued a DARPA contract with the project code name “HAVE BLUE,” to design, develop and build two demonstrator attack aircraft using LO technology to the greatest extent possible. The HAVE BLUE demonstrators were successful in proving aircraft LO technology was doable. In November 1978 the Air Force issued a production contract to Lockheed for the F-117, using the project name “SENIOR TREND.”
When the HAVE BLUE aircraft were being developed, Lockheed design engineers became aware of a Russian mathematician, Pyotr Ufimtsev, who wrote a scientific report in 1964 regarding the theory of RF energy’s behavior when it is transmitted at objects with varying geometric shapes. The Russian discovered that a radar target with a 90 degree right angle edge (i.e.; the wing, a fuselage side panel, the cockpit windscreen, jet engine intakes, et al) visible to the illuminating radar will return a stronger radar echo than if reflected off the side of a large aircraft. As it often happens with mathematical or scientific theory, it looks good on paper, but the practical ability to apply the theory in the real world has not quite caught up, yet. This was the case with Ufimtsev’s research; computer technology in 1964 was not advanced enough to apply Ufimtsev’s theory to the practical application of aircraft design. By 1975, however, computer science had advanced far enough that Lockheed could apply the Russian’s theory into the real world design of the F-117. Nearly all of the LO technology incorporated into the F-117 would find its way into the F-22 Raptor’s design.
Another word needs to be said about computer technology available in the mid-1960s vs. the late 1970s. Not only did the F-117’s design benefit from more advanced computer technology, but so did the plane’s aerodynamics. By avoiding right angle edges on the aircraft’s exterior, it made the F-117 aerodynamically unstable. As discussed earlier about the F-16’s aerodynamic instability, necessitating computer, fly-by-wire flight controls, if Ufimtsev had attempted to design a plane using his theory back in 1964, he would have been unsuccessful without fly-by-wire computer technology to keep the plane in the air. It would be another 11 years before computers had advanced far enough to keep an aerodynamically unstable aircraft airborne.
During the Top Secret HAVE BLUE demonstrator project, Lockheed and the Air Force both acknowledged the aircraft design had to be focused on maximum inclusion of LO technology in terms of development costs. In plain English, this meant the rest of the plane’s equipment and systems needed to be “off-the-shelf” from another DOD production aircraft to avoid the unnecessary cost of trying to make the F-117 a brand new aircraft from the wheels, up. Off-the-shelf examples used on the F-117 included: The F-16’s fly-by-wire flight control system, the A-10’s landing gear, the GE F404 jet engines from the F/A-18, and the C-130’s environmental control system.
Without a doubt, the most important contribution to the F-117’s miniscule RCS was the fuselage’s multifaceted surface. Based on Ufimtsev’s theory, Lockheed engineers designed the plane so that anyplace where one surface connected to another, it was not at a right angle. The final fuselage design appeared like an assortment of different-sized triangles. In an oversimplification, if a radar signal pinged the F-117 with its lack of right angle-joined surfaces, the reflected echo, as noted earlier with the tennis ball example, would deflect-off in a direction away from the transmitting radar. In addition to the radar deflection ability of the multifaceted skin, the RCS level was also reduced by using an internal bomb bay to avoid radar reflections from externally hung ordnance. The engine intakes and exhaust were buried in the two wing roots to avoid the typically strong radar echoes when they are externally detectable by radar. It also helped that the engine compressor blades (usually a strong radar return) were recessed enough to be undetectable. The final LO feature for RCS reduction was using a custom-designed black paint that absorbed radar emissions. The end result for the F-117’s minimized RCS value was an incredible 99% of all radar signals pinging the plane did not result in a detectable return signal back to the transmitting unit!
Rounding out the F-117’s LO technology…During the Cold War the Soviets developed two types of SAMs using Infrared detection and tracking of a target aircraft’s heat signature. One of SAMs was the SA-7 Grail (USSR called it “Strela”). The SA-7, known in today’s vernacular as a “MANPAD” (MAN Portable Air Defense), is an infrared, handheld, SAM introduced into the Vietnam War in 1972. As the North Vietnamese Army (NVA) pushed south across the DeMilitarized Zone (DMZ) into South Vietnam’s Quang Tri Province, they brought the SA-7 MANPAD with them. The SA-7 was ideal for shooting down low flying helicopters. During the NVA’s 1972 Easter Offensive, they were quite successful in shooting down South Vietnamese UH-1 “Huey” helicopters using the SA-7 to “home-in” on the IR heat signature of the Huey’s turbojet engine exhaust. The SA-9 Gaskin was also an IR homing missile transported on a trailer. The SA-9 was not used in Vietnam; but, it was quite conspicuous as an active component of Eastern Europe’s EOB.
The F-117’s IR countermeasures included burying the two engine exhausts in the wing root, and installing a vertical separator to diffuse the hot exhaust by breaking-up each exhaust duct into two parts before it cleared the aft section of the fuselage. In furtherance of a reduced IR heat signature, the engines were not fitted with afterburners; the plane was purely sub-sonic.
Since the F-117 was built to essentially penetrate an enemy’s denied airspace undetected by air defense radars, then it did not make sense for the aircraft to actively operate onboard R.F. transmitters, such as: radios, radar, IFF transponders, etc, during target ingress, egress, and weapons targeting & release. Nearly all F-117 mission sorties were flown blacked-out, at night, to avoid visual detection as an added stealth feature to the plane’s almost non-existent radar & IR signature.
In the F-117’s -1 flight manual, TO 1F-117A-1, Section IV, regarding operation of the aircraft’s Auxiliary Equipment, it says: “The integrated avionics configuration of the F-117A has been carefully selected to maximize the effectiveness of the aircraft without compromising the advantages gained by its special capabilities (i.e.; Low Observables Technology).” The same section of the -1 manual went on to say: “Passive operation in the infrared portion of the spectrum has been selected as the most viable sensing method. It yields the highest resolution possible with aperture requirements that can be accommodated within the special design requirements.”
When you decipher the foregoing flight manual verbiage, it’s telling us the Air Force wanted to avoid the use of any avionics that transmitted a R.F. signal. In a nutshell, the aircraft designers wanted to avoid generating enemy-detectable ELINT. On most military aircraft the greatest source of ELINT is radar equipment. The F-117 didn’t have any radar equipment for search, tracking, attack or terrain following. The only thing it carried was a typical radar altimeter which was low power, only useful at low altitudes, and was turned-off before entering hostile airspace. Navigation aids, such as TACAN and ILS (instrument landing system), the radios and the IFF transponder were also turned-off for the same reason. The primary mode of navigation was passive GPS, and ordnance delivery was done via IRADS (infrared acquisition & designation system). Lastly, the F-117 carried a passive RHAW (radar homing and warning) receiver; but, did not carry jamming equipment. The F-117’s LO technology and operating procedures became the future baseline of the F-22 Raptor.
Moving on to the second critical technology development coming out of Vietnam…active (as opposed to passive) EW equipment…
Referring back to the Alpha Strike bombing package used in Vietnam by the 7th Air Force, you will recall the use of jamming support aircraft; either accompanying the strike force, or as standoff jammers. When the ROLLING THUNDER bombing campaign started in North Vietnam in March 1965, the Air Force soon learned of the need to conduct ELINT collection and analysis of the enemy’s EOB. To that end, they deployed the Douglas EB-66C EW platform to Thailand. The EB-66C carried a crew of seven airmen: The pilot, navigator, chief EW officer, and four EWO crewmen. The pilot, navigator and chief EWO were seated up in the cockpit. The four additional EWOs had crew stations in the fuselage, occupying the space of the former bomb bay. The EB-66C’s primary mission was ELINT collection and analysis. The plane also carried seven jamming transmitters, but, they were not steerable. Standard ECM procedures of-the-day dictated that radar jamming was most effective if the jammer’s transmitting antenna was steered to point directly at the radar unit you were trying to jam. This meant the EB-66C was of limited value in a jamming support role.
USAF temporarily deployed some EB-66Bs standing NATO alert in Cold War Europe. The EB-66Bs were set-up in a special NATO configuration known as BROWN CRADLE, for use against Russian and the Eastern Bloc countries. The EB-66Bs did a passable job in Vietnam as an interim strike package jamming support platform; but, they were still lacking. Ultimately, the Air Force pulled two squadron’s worth of plain B-66s in mothballs at Davis-Monthan AFB, AZ., and fast-tracked the planes through a rushed modification program to make them EB-66Es with steerable antennas and the right mix of jamming transmitters for Southeast Asia. The plane was crewed by just a pilot, navigator and EWO. The plane carried 21 different jamming transmitters! In addition to jamming support planes, the strike package also required four other aircraft (usually F-4 Phantoms) to carry ALE-2, 4, 5 or 38 high capacity chaff dispensers. Third generation fighter-bombers were not designed with their own built-in chaff (or flare dispensers).
With all of the cobbled-together resources to complete an Alpha Strike without losing airmen, tactical air power experts searched for a means to reduce the risk of exposing so many fliers. In 1968 The Air Force awarded a contract under the classified project name, “COMPASS ROBIN,” to General Electric for the design and manufacture of two types of 2-channel noise jammers – the ALQ-71 and ALQ-72. The ALQ-71 covered 1-to-8 GHz, and the ALQ-72 covered the frequencies from 9-to-20 GHz. Third generation fighter-bombers were already space limited inside their airframes; so, GE designed external jamming pods for uploading on an aircraft’s under-wing hard point. Each pod weighed about 400 lbs.
I noted earlier that jamming technology was very much cutting edge stuff. It was difficult to produce, had a really long lead time, was very expensive, and it required constant repair by GE field engineers. Being constrained with these various issues, it left Air Force squadrons with an inadequate number of pods to put on every aircraft. It became accepted practice to put jammer pods on the lead fighter-bomber only.
Toward the end of the War, a newer jamming pod was made by then defense contractor AIL, a former division of the Eaton Corporation. AIL’s product, the ALQ-99, integrated the ALQ-71 & 72 into a single platform weighing 950 lbs and covered 1GHz to 20GHz. The ALQ-99 is also an under wing pod mounted on a hard point. One of the most important features of the ALQ-99 was the electronic interface between the plane’s RHAW equipment and the jamming pod. Based on the ELINT sensing of the RHAW, the ALQ-99 jamming system could either recommend or automatically select the most appropriate jamming response to defeat the radar system trying to track the plane. The auto-jamming feature was really important aboard single-seat fighter-bombers where the pilot was already task saturated with flying and fighting the aircraft. It is important to recognize, however, that EW technology in the 1970s & ‘80s was still not a complete “hands-off” process aboard an aircraft if the intent was maximum ECM effectiveness. Simply said, computer software & hardware technology was limited in terms of how much pre-programmed auto-signals analysis could be done effectively in a real-time ECM action/reaction scenario to consistently make the best jamming response.
Recognizing the technology limitations described above, the Navy responded by fielding a new genre of aircraft known as “Electronic Attack.” The EA-6B Prowler was the end result. The Prowler combined the roles of defensive jamming and offensive SEAD (the Wild Weasel role). In order to achieve maximum jamming effectiveness, the EA-6B carried multiple ALQ-99 pods and a dedicated team of three ECMOs (Electronic Countermeasures Officers). The ECMO supervisor sat next to the pilot in the right front cockpit, with the other two sitting side-by-side in the rear cockpit. The primary function of the rear cockpit ECMOs was managing the ALQ-99 system for the traditional defensive ECM role of ELINT analysis and the best jamming response.
The ALQ-99 is still the mainstay of the American military’s airborne defensive ECM. After 40 years the ALQ-99 jamming pod has been upgraded many times. The Navy’s newest electronic attack platform, the EA-18G Growler, carries the latest ALQ-99 version, the ALQ-99E.
When Northrop-Grumman and Lockheed-Boeing began engineering development on the B-2 Spirit and F-22 Raptor, respectively, the Air Force recognized the Alpha Strike bombing package used in Vietnam was a matter of necessity, not just a preference. To minimize the extensive use of support players, The B-2 and F-22 had to be designed for self-sufficiency. This led to both aircraft being developed with the ability to electronically defend itself. Taking this one step further, the electronic self-defense system envisioned for each aircraft had to be entirely contained within the plane’s fuselage to avoid the compromise of any stealth features.
For either a 3rd or 4th generation fighter, it would have been physically impossible to find the internal space to cram over 900 lbs of EW jamming equipment. When the Pentagon began researching the features needed in a 5th generation fighter, they were not looking to field an aircraft any larger than a 4th generation fighter. The F-22 is within +/- one foot in both fuselage length and wingspan of an F-15. The telling difference, however, is the F-15’s maximum weight is equivalent to the F-22’s dry weight. The F-22’s jet engines have 50% greater thrust. To a great extent, 4th generation fighters carried avionics designed and manufactured for certain finite capabilities and activities. In other words, if the designers needed the EW jamming equipment to perform a task, it had to be physically built that way. The more capabilities needed, the greater amount of equipment required. This is why the ALQ-99 multi-channel jammer weighed 950 lbs. Prior to the F-22’s development, the EW community knew what was needed to protect an aircraft in hostile airspace. The problem to be overcome was the hardware bulk for multispectral defensive jamming and limited computer technology.
In the 1990s the rapid rise in software and computer hardware technology began showing promise in ECM systems development. These improvements meant that software code could quickly change the jamming response; which, in turn, meant less single-purpose equipment in the jamming suite. Electronic systems development was using more capable integrated circuits, reducing the size of equipment. Between the vast improvements in software, which led to more multi-use equipment, and less dedicated hardware, plus, the overall trend of electronics miniaturization, it became doable for the F-22’s ECM gear to be carried completely inside the airframe.
In the final analysis, the Air Force finally had a fighter jet that could perform air-to-air combat and ground attack equally well. Its low observables made it undectable, and its ECM suite enabled the plane to electronically protect itself from airborne threats, and enemy ground-based threats. The F-22 Raptor is an aircraft that had been 50 years in the making.
Steve Miller, Copyright © 2012
The Best W.W. II Submarine Movie
What movies or TV series have you watched more than 5 times?
I’m a U.S. military historian and national security SME. Since 1998, I’ve made the effort to keep up with new war movies and t.v. shows as they are released. I cannot remember the last pre-1998 war movie or show that I’ve come across that I haven’t seen before.
I don’t like to critique the ones I watch, since even a poorly made movie/show is costly and requires hard work. That being said, my attitude is if you’re going to produce a war-related piece, at least put enough money and effort into it to avoid the common, amateurish mistakes.
Examples of obvious mistakes can be things like depicting a German W.W. II warplane that’s painted like a Luftwaffe plane, but it’s actually an American plane, or the production wardrobe supervisor used something from the Vietnam War in a 1st Gulf War movie.
With the above comments in mind, the best war movie that I’ve watched six times is the 1981 German film, “Das Boot” (The Boat). It’s the most accurate W.W. II submarine movie I’ve ever seen. The dialogue, interior set design, uniforms and the combat scenes are impeccable. The scenes of the crew undergoing relentless depth charge attacks are frighteningly realistic.
I first saw Das Boot in 70mm, Dolby IMAX. The soundtrack was deafening during the combat scenes, and the jarring, twisting, and crashing of the sailors and equipment inside the submarine wasn’t trick photography or other movie magic.
In order to make the movie, the production crew took hundreds and hundreds of photos and videos inside of a real W.W. II German submarine on display at a museum in downtown Chicago. Then the entire end-to-end internal compartments of sub were built as a complete 287 foot long set that was completely enclosed like a real submarine.
Most submarine movies simulate the extreme movements while under attack by manipulating the camera to capture the action, and then the actors are trained to move like they’re being thrown around inside the submarine when a depth charge is exploding. For Das Boot, the whole submarine tube set was mounted on a gimbaled, 3-axis full motion platform just like a flight simulator. The full motion platform eliminated the need for the actors to fake being thrown around after a depth charge explosion. The motion platform threw people around like the real deal.
For safety purposes, the actors had to be taught how to fall without getting hurt. They wore concealed padding and all of the equipment they could get injured on was foam rubber molded to the right shape and color.
Lastly, the film was made in German. The original release had English subtitles. It became so popular in English speaking countries that they brought the actors back to the studio a couple of years later and recorded an English soundtrack. The dubbing was painstakingly matched to the visuals. The main characters all spoke passable English with a German accent. The only exception was one of the supporting actors who had a fair amount of dialogue, didn’t have decent English skills. The producers hired an English tutor, but the recording and editing schedule was late and over budget, and the actor couldn’t assimilate enough English fast enough. So, they hired another actor to do the English voiceovers for the original cast member. The dubbing came out pretty good. You would have to intently focus on an actor’s mouth for several seconds to see a very slight difference in movement from German to English.
This is probably way more than anyone wants to know. Check it out on Amazon Prime Video…it’s worth the time to watch. Ciao!

The Politics of Having Your Cake and Eating It, Too
This article explores the transition and meaning of “Democratic Republic” as it was understood at America’s Founding, versus how it is viewed by many in 21st Century America. Without a doubt, there’s a stark contrast between the two eras, and the implications of it are concerning. Read on to learn more.
What is the definition of “The Politics of Having Your Cake and Eating It, Too?” The phrase was first used by former British Prime Minister, Boris Johnson, during the process of extracting Great Britain from the European Union, otherwise known as “Brexit.” Johnson opined, it is the “pursuit of mutually exclusive, incompatible political goals—specifically, trying to secure the benefits of a decision while avoiding its necessary, often negative, costs.” Johnson further stated, “the phenomenon regarding ‘cakeism’ implies keeping advantages while rejecting obligations.”
The Founding Fathers of the United States wrote the Declaration of Independence and the Constitution explicitly to enshrine life, liberty and the pursuit of happiness in perpetuity. Their concept of these principles in life, and in politics, were based on fair, moral and ethical principles.
These principles enable democracy to work based on majority rule, as intended. Democracy and majority rule decays when the enabling principles lose their influence on politics and society. What emerges are two truths that define “The Politics of Having Your Cake and Eating It, Too:”
1.) Majority rules might be the hallmark of democracy, but increasingly, people in the political and societal minority are insisting that they should have a niche carved-out of the majority to still get their way.
2.) A growing number of people in America are embracing a socialist agenda, looking for government at all levels to provide solutions to supposed “problems” they perceive as not being acted on. Conversely, the same socialists want the government to step back on issues meaningful to them, but not the mainstream public.
By definition, neither of these two truths can exist without having your cake and eating it, too; which is incompatible with democratic, majority rule.
A simple way of looking at the “The Politics of Having Your Cake and Eating It, Too” is the old political phrase, “you can please all of the people some of the time, and some of the people all of the time, but you can’t please all of the people all of the time.” American politics in the 21st Century has become a selfish quagmire of pushing to get what you want all of the time, and not care what or if anyone else wants.
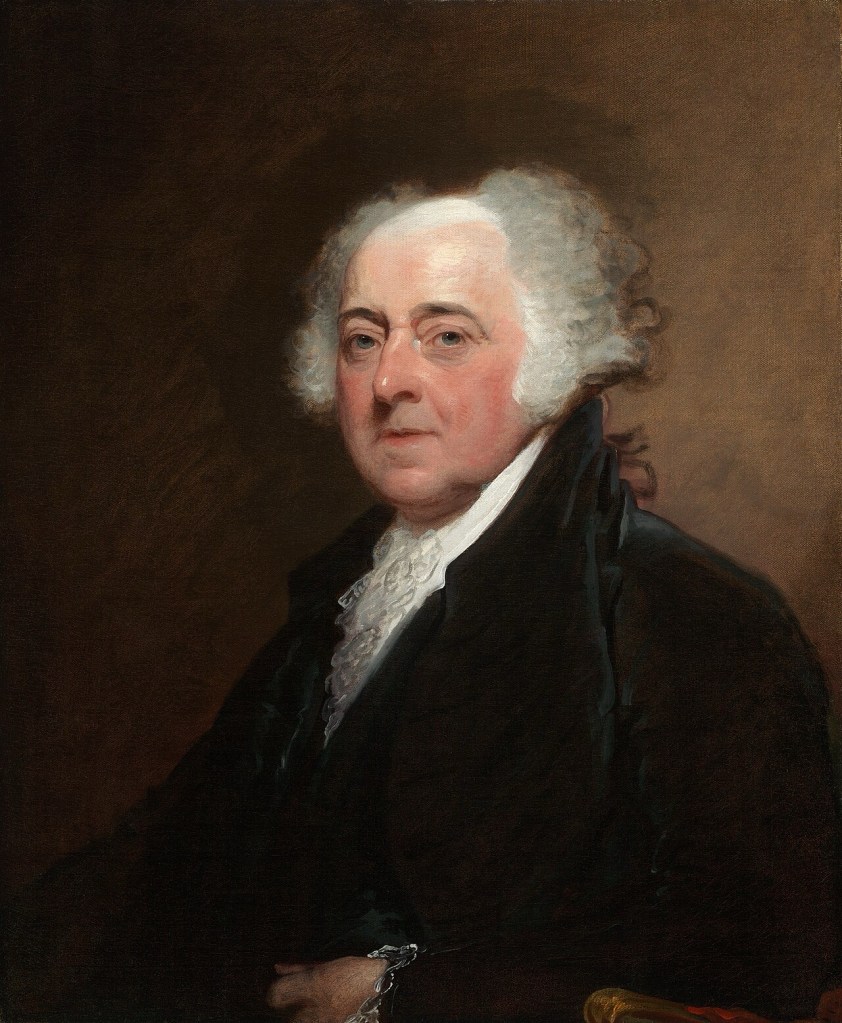
Keep in mind the following quote by John Adams; it will be important later in the story.
“We have no government armed with power capable of contending with human passions unbridled by morality and Religion. Avarice, ambition, revenge, or gallantry, would break the strongest cords of our Constitution as a whale goes through a net. Ours is made only for moral and religious people. It is wholly inadequate to the government of any other kind.”
Introduction
This topic requires some historical perspective on America’s original 13 colonies. In modern times, the founding of the United States of America is often thought of as a tight knit group of colonies (states) that equally despised the British Crown and its government. The reality was different.
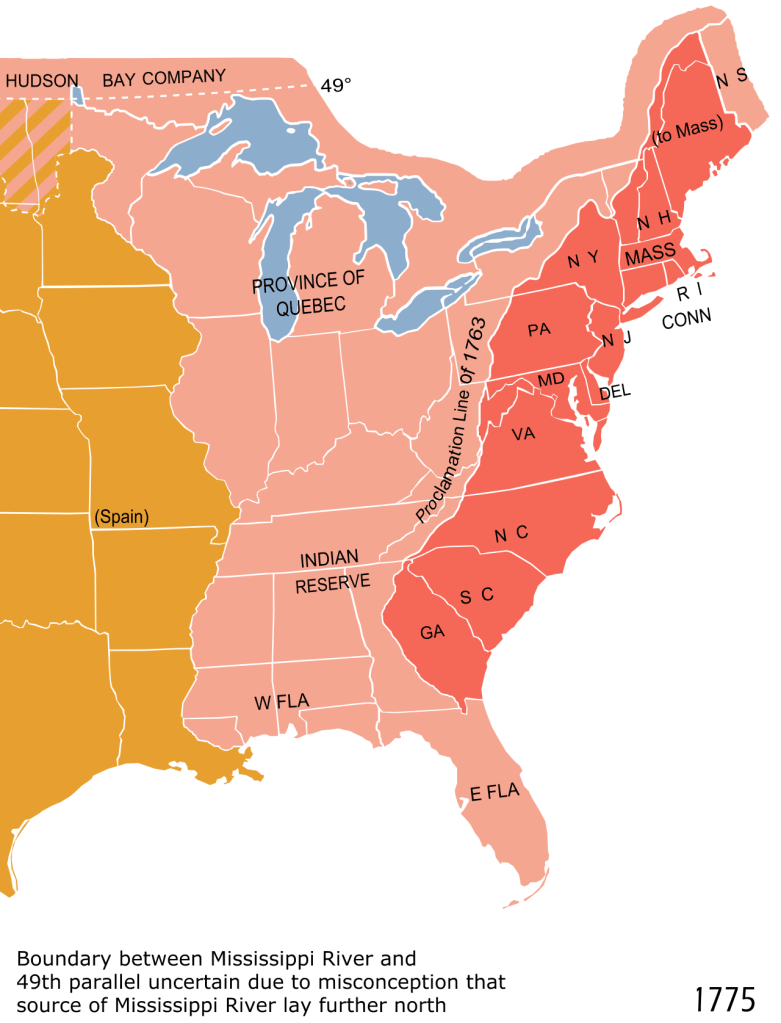
Each colony had its authority and legal right of existence from the King of England in the form of a written charter. To be clear, each colony had its own, separate charter. The charters did not create any legal ties by the Crown between one colony and another. Each one had its own government and elected officials.
There was one exception, however, to elected officials throughout the colonies: Each colonial governor was appointed by the British Government. It was common for governors to reside in England, and then move to America to assume their duties. British Governorships were common practice for all colonies worldwide.
It’s a bit ironic that even though the colonists were officially British citizens, the vast majority had never been to England, often spanning several generations. Colonist allegiance to the Crown was a mixed bag of staunch loyalists, ambivalent citizens (not necessarily disloyal), American independence sympathizers, and staunch supporters of American independence. Aside from the well known Founding Fathers, you could not be sure of someone’s feelings about the War for Independence.
A further twist to the story was that the 13 colonial charters were not issued for the same purposes. For example, the Pilgrim’s charter for Massachusetts was granted for religious autonomy from the Church of England. The Virginia colony established at Jamestown was for commercial purposes to make money for the British Crown.
The colonies were definitely not based on a cookie-cutter model. Some colonies, such as New York, Virginia and Massachusetts, were quite prosperous. In any event, they all did business with each other to one degree or another, and were relatively contented with their lot in life through the 1750s.
During this timeframe the British fought the French & Indian War over the control of Canada, and the unsettled areas around the Great Lakes. The British won the war. Future President, George Washington, was an officer fighting for the British. Other colonists also fought for the British, but mostly as militiamen.

The war was not fought on behalf of the colonies. In general, the colonists who fought in the war, did so as loyal subjects of the Crown. In fact, Washington’s desire was to become a professional officer in the British Army. Promises made to him by British generals were reneged. This left a bad taste in Washington’s mouth; it was a lesson he never forgot.
Although the British won the French & Indian War, the government was left with massive debts. Nothing was said about the war in relation to the colonies, but it soon became apparent in the early 1760s. Under the direction of the King, laws were passed affecting just the American Colonies that began imposing taxes on numerous things.
After making some inquiries, the colonists were told that the taxes were being levied to pay British war debts. Now, all of a sudden, the colonists learned that the Crown was saying the French & Indian War was actually fought on behalf of the 13 colonies, so it was only fair that they should contribute to servicing the debt!
This “taxation without representation” situation referred to the British Parliament passing the tax laws, but was bereft of any membership from the Colonies. It may not have been clear to the colonists in the 1760s, but hindsight by future generations would come to know that the hated taxation was actually the beginning of the end to British Rule in America.
What Happened Next?
Independence was declared on July 4, 1776, and the Founding Fathers dispersed to their Congressional duties during the war. James Madison and a couple of delegates broke-off to start drafting the document that would define the parameters of a new government.
The Founding Fathers who signed the Declaration of Independence were prominent members of society; some were more well-to-do than others. The most common denominators were: significant land holdings and business interests, including: farm owners, bankers, merchants, attorneys, import-export traders, and politicians.
The Founders were also well educated. Many of them were connoisseurs of books with impressive personal libraries. The U.S. had an impressive inventory of books in the Library of Congress; that is until the British Army burned it down in the War of 1812 and lost its entire collection. Upon his death in 1826, Thomas Jefferson bequeathed his whole book collection to Congress. The Jefferson collection was the largest one in the U.S. for its time, and easily surpassed the size of the Congressional Library prior to its burning.
James Madison and other patriots were well-versed in the “Classics” taught in a liberal arts education. This included studying the ancient governments of the Roman Republic, Sparta, and Athens. There were significant writings on politics, ethics, and societies, by famous scholars, including: Socrates, Aristotle, Plato, John Locke and Edmond Burke.
The importance of the Founding Father’s liberal arts education cannot be overstated. The work of standing-up a sovereign country and a new government – a democratic republic – was a serious undertaking. They learned from the Classics that if they did not favor a constitutional monarchy, such as what they were living under as British subjects, with known civil and human rights restrictions, then they needed to know what and how to create something better.
It was not good enough for the colonists to simply dislike the British Government. The Founders understood the need for a new government that was serviceable and avoided the miscues of previously felled ancient democracies like Rome. This would be a tall task because it exposed the significant differences of opinion on state’s rights versus a strong central government. The colonies were not ready to surrender their staunch self rule.
It took Madison several years to complete the first governing document. Their work yielded a document entitled the “Articles of Confederation.” Whereas, the eventual U.S. Constitution was written over the summer of 1787, the Articles of Confederation took several years due to the exigencies of wartime.
A key factor in slowing the writers was the British Army’s vigilance in seeking the arrest of the Declaration of Independence signers; they were considered traitors by the British Crown. If any of them got caught, they would likely be imprisoned for treason. This made out-of-town travel quite precarious, thus impeding the writing of the Articles of Confederation.
The Articles of Confederation were seriously flawed. The scales of politics were heavily weighted toward state’s rights. The postwar need for a strong central government was not yet apparent. The Articles were ratified and took effect in 1781 while the war continued. Within a couple of years, the Articles’s flaws were painfully evident. In 1787, four years after the war ended, the Constitutional Convention was convened in Philadelphia to fix the problems with the Articles of Confederation.
The convention goers pivoted to writing an all new document and scrapped the Articles of Confederation. The new U.S. Constitution was ratified by the states in 1788-1789. Elections were conducted and George Washington took office as the first President of the United States of America in March 1789.
James Madison was elected to Congress and set about fulfilling his promise to write a Bill of Rights as the first 10 amendments to the Constitution. The Bill of Rights ensured the Declaration of Independence’s precepts of the right to life, liberty and the pursuit of happiness, were codified in the Constitution.
Circling Back to John Adams’ Quote
Not withstanding the poor treatment of African-American slaves and Native Americans, none of the colonists needed an explanation of the meaning behind “the right to life, liberty, and pursuit of happiness.” It was understood by everyone that your right to life, liberty and pursuit of happiness could not impinge upon another person’s rights, and vice versa. It was also understood that in a democratic republic, decisions were made based on majority rule.
As John Adams expressed, you cannot properly ensure people’s rights, if they do not believe in religious tolerance, nor for the need of ethical and moral conduct. Throughout America’s 250 years of existence, but especially in the last 60+ years, society has become less and less desirous of upholding the rule of law, honoring democratic rights, or seeing the benefits of organized religion. These acts of selfish behavior came into full bloom at the start of the COVID-19 Pandemic in 2020, and has continued apace ever since.
The Rights and Responsibilities of American Society in the 21st Century
The following chart will start the discussion…
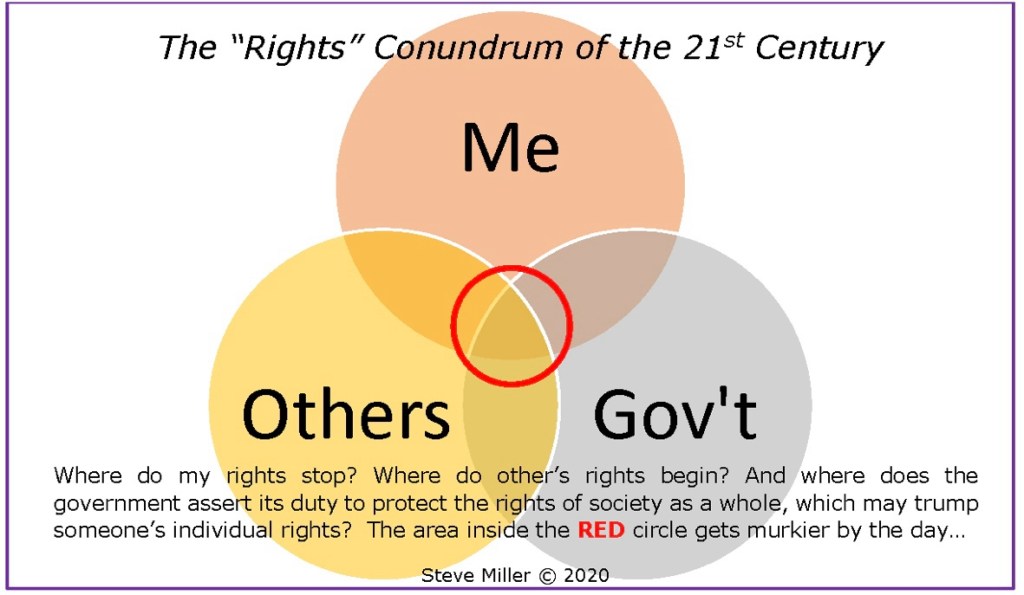
The funny thing about the Rights Conundrum is as the murky red circle expands, each of the three entities begin having less and less respect for the other two, and feel they have to stand-their-ground, not yielding anything, regardless of being right or wrong.
Key factors in this growing lack of respect in America includes: inadequate critical thinking and poor decision making skills. These dysfunctional factors have a strong relationship with an over-reliance on the First Amendment’s “right to free speech.” A common argument by some is the notion that the right to free speech means you should speak-out or act-out on any topic of your choice, anywhere, anytime, and to anyone you choose.
People would do well to speak when spoken to, and be measured in their speech when not asked directly to do so for a valid purpose. First Amendment free speech is a right, not a mandate.
A short phrase that is easily remembered in regards to speaking out-of-turn is: “Opinions offered, but not asked for, are likely to be more important to you, than to the person(s) receiving it.”
How Does This Affect 21st Century America?
Why is unchecked speaking or acting out trending upward, and why is it of concern to the American public? It has a lot to do with wisdom, discernment and judgment. There is an insidious faction in America exploiting the right to free speech. The danger of this is expressed below.
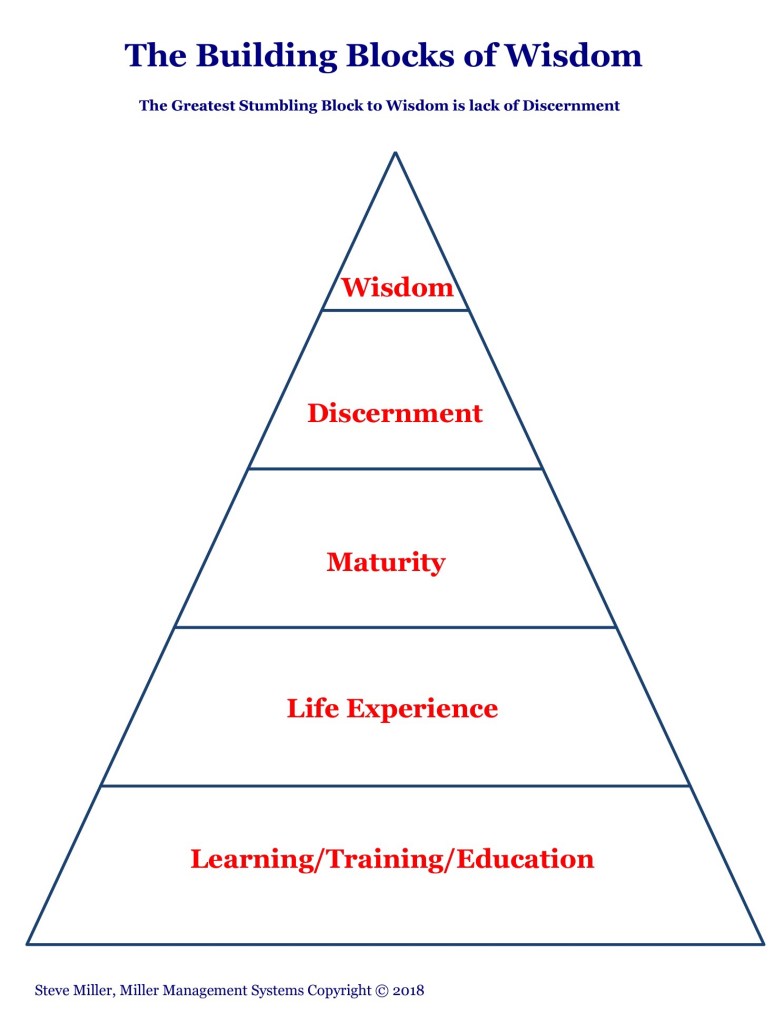
Acquiring wisdom is a building block process; there are no shortcuts. There are people lacking the building blocks, yet will still make decisions based on flawed judgment. And there are people with an education, adequate life experiences and maturity, leading to the top two building blocks. Yet, they erroneously believe they have everything needed to pass judgment, mistaking it for the exercise of wisdom. They would be wrong.
You cannot exercise wisdom if you have not applied an appropriate amount of discernment. Discernment must replace judgment. Discernment has, and judgment lacks, the ability to logically weigh alternatives and distinguish between informed choices.
Judgment makes it too easy to condemn things or people based on flawed information. Chronically poor judgment can lead to profiling, labeling, stereotyping, segregating, and discrimination, which can polarize societies, create anger and divide communities of all sizes. Judgment, rather than discernment, leads to unnecessary extremes that are far apart regarding a central topic.
Judgment without discernment and wisdom, is a necessary precursor to the politics of having your cake and eating it, too.
It is far less likely for someone to press for undemocratic policies and laws if their building blocks of wisdom are fully developed and serviceable.
Serviceability is important because there are people who have fully developed their powers of discernment and wisdom, but will selectively choose not to use them.
The simplest “tell” of someone seeking to have their cake and eat it, too,k in politics is their opposition to an issue supported by the majority, but cannot articulate a reasonable alternative solution.
Let’s Recap for a Moment…
- In discussing the “The Politics of Having Your Cake and Eating It, Too,” it manifests itself in two truths that define the concept. First, political and societal minorities are insisting that a niche be carved-out in-spite of an issue already ruled in favor of a majority. This truth has been successful on several significant issues.
- Secondly, growing political minorities are embracing socialism, looking to the government for solutions to perceived problems they feel are important enough to warrant legislation. Conversely, the same socialists want the government to back down on issues meaningful to them, but not the mainstream public. Examples of this include the nationwide antisemitic protests and the violent immigration enforcement obstruction protests.
- Neither of these two truths can exist under normal circumstances. But, if “The Politics of Having Your Cake and Eating It, Too” is aggressively pursued by the minority, then what seems impossible and incompatible with the democratic majority, may actually come to pass.
- President John Adams pointed out that the U.S. Government was established purposely for a nation of people with moral values and a belief in a power higher than a mere mortal. If someone uses their free agency to reject these principles, the government has little power to do anything about it.
- The Founding Fathers wanted to stand-up a government for their new country that avoided many of the flaws and pitfalls of previously failed nations, as well as, monarchies and dictatorships. They witnessed just how tricky it could be in creating a new government when the Articles of Confederation proved to be problematic. Even when the Constitution was rolled out, it did not include any civil rights provisions.
- Constitutional Convention delegates wrestled with including civil rights, but chose not to, out of concern that it would further delay getting draft copies of the Constitution out to the states. It was expected that ratification could take up to a year to get done. The delegates rationalized that the state constitutions already covered civil rights, so a Bill of Rights for the U.S. Constitution could wait. James Madison observed that each state’s civil rights provisions were different, but he would correct that by the first ten amendments to the Constitution during his first term in Congress.
- The Rights Conundrum noted that the American Government, individuals, and an unknown number of groups, were losing or denying the respect of others, and are disinterested in finding any common ground, unyielding, regardless of being right or wrong.
- First Amendment right-to-free speech is being distorted by the idea that anyone can say anything they want at any time, yet try to deny the right-to-free speech of others.
- Many in the American public are incorrectly passing judgment on a multitude of people and issues, using little or no discernment or wisdom.
Where Does This Toxic Brew Lead Us?
Thomas G. West, PhD, of Hillsdale College wrote an article entitled “The Political Theory of the American Founding.” West discusses the Founders take on Natural Rights, Public Policy, and the Moral Conditions of Freedom. The Founders were greatly concerned about how these issues would play out in a newly formed country and government.
In my July 2020 article entitled, “Defending the U.S. Against Foreign & Domestic Enemies,” I noted, “In simplest terms, our Founding Fathers recognized they were creating a nation with more citizen freedoms than any country on Earth, past or present. Prior to the American Revolution, there had never been a constitutional republic operated solely of the people, by the people, and for the people. All previous efforts to create this sort of nation-state ultimately failed, largely due to internal upheaval. The Founding Fathers recognized the democratic freedoms they hoped to create could be abused & breed internal subversion and violent insurrection.”
“For more than a decade prior to 1776, there were violent and divisive elements at work in the 13 colonies, intent upon keeping the oppressive yoke of the British Crown over everyone. This concern was memorialized and enumerated in the list of grievances noted in the Declaration of Independence. It was the first document of lasting importance to denounce the practice of fomenting domestic enemies, to wit in reference to King George: “He has excited domestic insurrections amongst us…” America’s first leaders had no reason to believe that by simply declaring their independence, enemies bent on fomenting domestic subversion and insurrection would stop such actions.”

The concern about domestic security led Five-star General of the Army, Douglas MacArthur, to say the following:
“I am concerned for the security of our great Nation; not so much because of any treat from without, but because of the insidious forces working from within.”
Prominent figures in American history would tell you the same thing that General MacArthur said. This would include George Washington, John Adams, James Madison, Abraham Lincoln, Theodore Roosevelt, and Woodrow Wilson. In the past 100 years, the likes of Franklin Roosevelt, John Kennedy, Ronald Reagan, and George W. Bush, would all express their concerns about homegrown radicalism, domestic espionage and fomented insurrection.
After the Constitutional Convention in 1787, a discussion ensued between Washington, Adams, Madison, Alexander Hamilton, and John Jay (the soon to be, first Chief Justice of the Supreme Court). The topic of the meeting was what steps could be taken to mitigate the state ratification committees getting bogged down in over analyzing the draft Constitution.
The five men decided the best way to avoid ratification problems was to publish a set of essays that explained the rationale behind various topics in the Constitution. The essays totaled 85, and became known as the Federalist Papers. Alexander Hamilton wrote more than half of them, followed by James Madison and John Jay. To avoid public focus on the authors instead of the paper’s contents, they used a nom de plume, “Publius,” a respected aristocrat and politician who was instrumental in forming the Roman Republic around 509 BC.
The Federalist Papers have been an invaluable resource to scholars and political scientists for over two centuries. The Papers are heavily used by the U.S. Supreme Court as a check on their rulings to mitigate the possibility of drifting away from the Constitution’s original intent. Rather than interpreting the Constitution to mean something different, thereby creating Case Law in lieu of legislation or Constitutional Amendment (such as the Court’s original 1973 Roe v. Wade ruling), the Federalist Papers help the Government to stay within established legal boundaries of making changes. An oversimplified example would be the long standing definition of what a “dog” is, and the Court rules that a dog is now reclassified as a hyena!
Back to the Federalist Papers, and the issues with domestic insurrection and civil unrest. James Madison was the ghost writer of Federalist Number 10, which dealt with “The Union (meaning the Constitutional Republic) as a Safeguard Against Domestic Faction and Insurrection.”
Considering that one of the colonist’s main grievances with the British Government was planting espionage agents throughout the Colonies to stifle the independence movement, there was no reason to believe that disruptive factions would automatically go away and never occur again. Federalist Number 10 explained how the proper use of the Constitution would mitigate factions attempting to use unscrupulous tactics to bend the public will in a direction that was counter to what was legally, morally and ethically acceptable.
An important point in understanding how factions come to be is, whether they are instigated overtly or covertly, they all start with one or two people, and then others are convinced to join them. The originator’s real motive(s) are often disguised.
Numerous safeguards were built into the Constitution to mitigate factions detrimental to the Government and/or the American public. Two of the most important safeguards are: establishing separate branches – Congress, the Presidency and Supreme Court – and the Electoral College scheme for electing the President.
The Electoral College was created in lieu of direct, popular voting. This system prevents a candidate or a zealous, malign faction, from trading “favors” for votes.
An example from back in the day is a candidate’s agent contacting a constituent-farmer to inquire about his family and farm’s general welfare. The farmer tells the agent that his greatest concern was not having enough hay to feed his livestock over the winter. He indicates that his misfortune stemmed from a poor yield of his own crop of hay. The election agent offers to have a wagonload of hay delivered to his barn. Incredulous, the farmer expressed his gratitude and asks how he can return the favor? The agent says he would like to count on the farmer’s vote for the candidate he represents in the coming election? The farmer agrees to cast his ballot as requested.
The second purpose of the Electoral College is to curb the influence of voters in the growing, large urban populations, which would tend to overshadow rural voters. It is unlikely the Constitution will ever be amended to eliminate the Electoral College and replace it with a regular, popular vote system.
It can be seen today in states with large urban population centers. Of the 15 largest U.S. cities, only Ft. Worth, TX and Jacksonville, FL are mostly conservative. At a state level, 14 states typically vote liberal in national elections. The liberal states are located on the West Coast, upper Midwest and the Northeastern states. The inland states are mostly conservative. Eliminating the Electoral College would disenfranchise voters in 70% of the states, in favor of the 14 states with the largest liberal voter blocks.
This is not a liberal vs. conservative issue; it’s just stating the reality of the situation. The non-partisan nature of this situation is evidenced by the fact that when the Constitution was written, there were no political parties, nor a bifurcated voter electorate.
A Word About National Security Implications
The covert espionage campaign waged by the British Crown during colonial times was not a phenomenon of an 18th Century monarchy; it happens worldwide today. Consider the following two statements originating from a foreign country:
“By inserting disinformation in publications, including social media, advocating extremist ideas, inciting racist and xenophobic flashmobs, conducting interstate computer attacks on the critical infrastructure targets that are vital for the functioning of a society, it is possible to “heat-up” the situation in any country, all the way up to the point of fomenting social unrest.”
– Igor Dylevsky, Major General, Deputy Chief of Operations, Russian Military General Staff
And,
“It is necessary to inculcate in the psyche of intelligence agents who conduct clandestine operations, the belief that morals and social norms mean absolutely nothing for intelligence work.”
– The Qualities of an Intelligence Agent, Russian Espionage Training Manual
The foregoing statements are not the exclusive purview of America’s adversaries. The protests during the Covid Pandemic, the Antisemitic Rallies of 2024 or the Anti-Immigration Protests over the past year were not fomented by foreign adversaries; the organizers were American citizens and lawful Permanent Legal Residents.
The real malaise of the “The Politics of Having Your Cake and Eating It, Too” is a perfect tinderbox just looking for a match. This malaise fosters the following things:
- Open disrespect for the majority; #
- Contempt for authority; #
- Name calling that incites violence, causing property damage, unnecessary injury, and sometimes even death;
- Insistence that there may be a majority and a minority, but an individual still wants what they want;
- Making immoral and unethical demands for free speech, yet denying the free speech of others;
- Railing against the Government on one issue, but expect it to support you on other things;
- Shuns accountability when it’s not in their interest.
These seven points of malaise, or problematic behavior, didn’t happen overnight. Prior to the Baby Boomer generation, none of these things were common in America; it changed for the Baby Boomers during the Vietnam War era. The two problems listed at the top with an adjacent # sign, first appeared in the 1960s during the Vietnam War protests. The other five points of malaise are beyond the value system the Baby Boomers grew up with.
Much has changed in all aspects of American life during the timespan from the 1970s through the 2020s. American society, culture, higher education, and Federal Government, have changed so much – including extreme polarization – that these institutions now have environments to support, or at least be indifferent to, the politics of having your cake and eating, too. A key factor in all of this is the corruption of personal behavior. None of the last five points of malaise would have blossomed as they have without the decay of individual morals and ethics.
America will never be perfect, including the government, but it’s the best one amongst the lot of some 200 countries. The good in this country far outweighs the bad. There are two things I always keep in mind about our country and how we go about our daily lives as Americans. I must confess that the following two quotes are not mine, but I wholeheartedly believe in them; they were borrowed from a prominent Christian denomination:
- We believe in being subject to kings, presidents, rulers, and magistrates, in obeying, honoring, and sustaining the law.
- We believe in being honest, true, chaste, benevolent, virtuous, and in doing good to all men; indeed, we may say that we follow the admonition of Paul—We believe all things, we hope all things, we have endured many things, and hope to be able to endure all things. If there is anything virtuous, lovely, or of good report or praiseworthy, we seek after these things.
If we could keep these two thoughts in mind, which align with President Adams admonition, our country and ourselves would be in a much better place. When we, and American institutions, disregard morality and fail to remember our country was founded on the principles of religious tolerance, our personal and collective futures are very much in doubt.
In 2026, is America the same, grand, Democratic Republic of 250 years ago? I am hard pressed to say “yes.”How about you? Maybe America can get past “The Politics of Having Your Cake and Eating It, Too” by focusing less on the individual, or factions of dubious origin, and more on ethics, morality, and the very real dangers expressed by General MacArthur.